


Equipo Shieldworkz
NERC CIP-015 & Monitoreo interno de seguridad de red (INSM): Tu guía para una seguridad OT más sólida
Imagina esto: un atacante sofisticado se cuela por tu firewall, tus defensas perimetrales resisten, pero dentro de tu zona de red confiable, un malware mapea en silencio tus PLC, altera puntos de ajuste y espera. No suena ninguna alarma, porque solo estás vigilando los bordes.
Ese escenario ya no es hipotético. Las amenazas actuales de Seguridad OT prosperan con el tráfico “este-oeste”, es decir, las comunicaciones que ocurren dentro de tu Perímetro de Seguridad Electrónica (ESP). Precisamente por eso la North American Electric Reliability Corporation (NERC) introdujo CIP-015-1 y su enfoque en el Monitoreo interno de seguridad de red (INSM).
Como siempre, antes de seguir, no olvides consultar nuestra publicación anterior sobre la siguiente jugada de Handala: de "hack-and-leak" a "asedio cognitivo"aquí.
Como gerente de planta, ingeniero OT o CISO responsable de infraestructura crítica, ya conoces lo que está en juego: el tiempo de inactividad cuesta millones, las multas regulatorias se acumulan rápido y una sola brecha puede desencadenar apagones o incidentes de seguridad. En esta guía detallada, te llevaremos paso a paso por lo que realmente significa NERC CIP-015, los principales riesgos de protección de redes ICS que enfrentas ahora mismo, los pasos prácticos para implementar INSM y, lo más importante, cómo la plataforma impulsada por IA agente de Shieldworkz hace que el cumplimiento sea sencillo mientras brinda defensa de infraestructura crítica en tiempo real.
Por qué la seguridad perimetral tradicional se queda corta en entornos OT
Durante años, los equipos OT dependieron del enfoque de “castillo y foso”: firewalls robustos en el ESP, reglas estrictas de conectividad externa enrutable y la esperanza de que nada malo entrara. Pero los atacantes modernos no solo tocan la puerta principal. Usan compromisos de TI, vectores de cadena de suministro o acciones internas para aterrizar dentro de tus zonas confiables y luego moverse lateralmente.
El tráfico este-oeste, es decir, las conversaciones entre PLC, RTU, HMI, sistemas SCADA y sensores IoT, se ha convertido en la nueva superficie de ataque. Y como estos dispositivos a menudo ejecutan protocolos heredados con seguridad incorporada limitada, una vez que un atacante entra, puede mezclarse con las operaciones normales.
Los datos recientes dejan claro el punto. En 2025, el 96% de los incidentes de seguridad OT se originó en compromisos a nivel de TI, y el 60% de las organizaciones experimentó al menos un incidente OT. Los ataques de actores estatales y hacktivistas contra infraestructura crítica se duplicaron en comparación con 2024, y el ransomware sigue causando interrupciones operativas reales en los sectores de energía eléctrica, manufactura y energía.
Las herramientas perimetrales simplemente no pueden ver lo que sucede dentro de tu red. Esa brecha de visibilidad es lo que NERC CIP-015 fue diseñado para cerrar.
¿Qué es NERC CIP-015? El estándar que cambia las reglas del juego
Aprobado por la Federal Energy Regulatory Commission (FERC) el 26 de junio de 2025 (vigente a partir del 2 de septiembre de 2025), NERC CIP-015-1 es el primer estándar de confiabilidad que exige Monitoreo interno de seguridad de red (INSM) para los sistemas cibernéticos del Bulk Electric System (BES) de alto y mediano impacto.
En lugar de enfocarse solo en el tráfico norte-sur que cruza tu perímetro, CIP-015-1 requiere que monitorees, detectes y analices la actividad dentro de zonas de red confiables. El objetivo es simple pero poderoso: detectar comportamiento anómalo temprano para que puedas responder antes de que haya consecuencias físicas.
Requisitos principales de CIP-015-1 (R1–R3)
El estándar se reduce a tres mandatos claros para los sistemas cibernéticos BES aplicables:
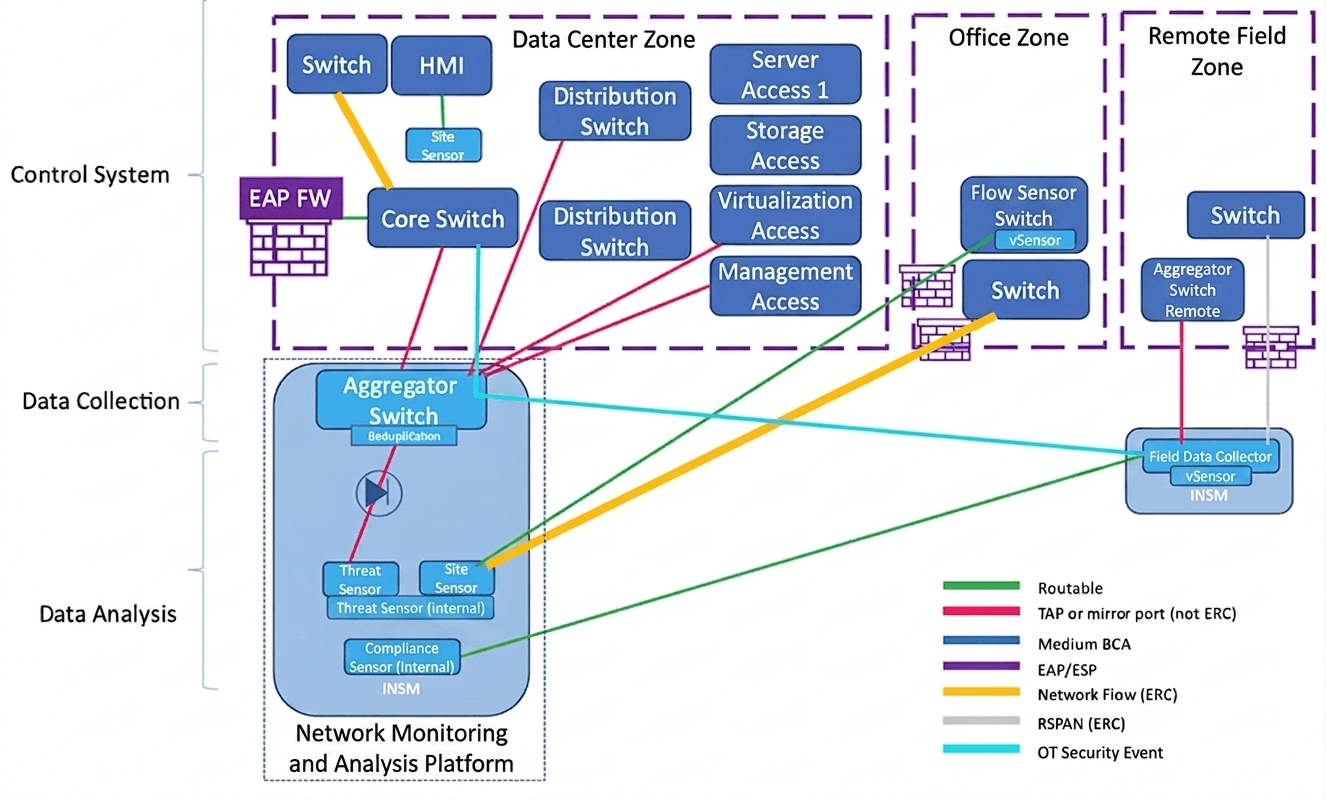
R1: Recopilación, detección y análisis Debes implementar fuentes de datos de red para recopilar información sobre conexiones, dispositivos y comunicaciones. Usa un enfoque basado en riesgos para detectar actividad que se desvíe de tu línea base normal. Después evalúa las anomalías para decidir si se requiere respuesta o mitigación.
R2: Retención de datos Conserva los datos de INSM vinculados a anomalías detectadas hasta que concluyan las investigaciones o acciones.
R3: Protección de datos Protege todos los datos de monitoreo recopilados y retenidos contra eliminación o modificación no autorizada.
Estos requisitos están diseñados intencionalmente para enfocarse en resultados. NERC no prescribe herramientas exactas; solo exige que tu solución proporcione monitoreo continuo y pasivo sin interrumpir los procesos OT sensibles al tiempo.
El poder del Monitoreo interno de seguridad de red (INSM)
INSM no es otra solución puntual: es una capacidad. Cambia tu postura de Seguridad OT de una defensa perimetral reactiva a visibilidad proactiva dentro de la red.
A diferencia de las herramientas basadas en firmas que buscan malware conocido, INSM se basa en la línea base: aprender cómo se ve lo “normal” en tu entorno único, hasta llegar al tráfico de protocolos entre PLC específicos. Una vez establecida la línea base, cualquier desviación (un nuevo dispositivo, un comando inusual, un flujo de datos inesperado) activa la detección.
Este enfoque es ideal para OT porque es pasivo. No hay agentes en dispositivos heredados frágiles. No hay riesgo de interrumpir la producción. Solo visibilidad profunda y contextual del tráfico este-oeste en todo tu entorno ICS.
Las principales amenazas actuales que apuntan a redes ICS e IoT
Ya sientes la presión. Esto es lo que realmente está ocurriendo en el mundo real:
Movimiento lateral después de un compromiso de TI: Los atacantes entran mediante phishing o la laptop de un proveedor y luego se desplazan silenciosamente dentro de tu zona OT.
Ataques a la cadena de suministro y al firmware: Las actualizaciones comprometidas o los dispositivos de terceros introducen puertas traseras persistentes.
Amenazas internas y errores de configuración: Un empleado descontento o un simple error humano pueden abrir puertas que las herramientas perimetrales nunca ven.
Ransomware con impacto en OT: Los grupos ahora entienden los protocolos industriales y atacan deliberadamente los procesos para causar la máxima interrupción.
Preposicionamiento de actores estatales: Actores sofisticados mapean hoy tus lazos de control para poder actuar mañana.
Las cifras son preocupantes. Más de 3,300 organizaciones industriales enfrentaron ransomware en años recientes, y las nuevas variantes de ransomware con conciencia OT siguen en aumento. Solo los dispositivos IoT registran 820,000 ataques diarios. Sin INSM, estas amenazas pueden permanecer sin detectarse durante meses.
Paso a paso: cómo implementar INSM para cumplir y proteger de verdad
Implementar INSM no tiene por qué ser abrumador. Aquí tienes un plan práctico:
Mapea tu entorno Comienza con un descubrimiento completo de activos: cada PLC, RTU, switch y sensor IoT. No puedes establecer una línea base de lo que no ves.
Establece líneas base basadas en riesgo Captura patrones normales de tráfico durante semanas (o meses para operaciones estacionales). Concéntrate primero en los sistemas cibernéticos BES de alto impacto.
Implementa monitoreo pasivo Usa taps de red o puertos SPAN para alimentar los datos a una solución INSM dedicada. Asegúrate de que admita protocolos industriales sin introducir latencia.
Habilita la detección y el análisis de anomalías Configura alertas automáticas para las desviaciones. Crea flujos de trabajo para que tu equipo pueda evaluar rápidamente si una anomalía requiere investigación.
Gestiona la retención y la protección de datos Automatiza el almacenamiento seguro y la protección contra alteraciones de los datos relacionados con anomalías para cumplir con R2 y R3.
Integra con los procesos existentes Alimenta los hallazgos de INSM a tu SOC, tu plan de respuesta a incidentes y tus reportes de cumplimiento.
Prueba y ajusta continuamente INSM es un programa, no un proyecto de una sola vez. Revisa las líneas base cada trimestre conforme evoluciona tu red.
Calendario de implementación: no esperes para comenzar
1 de octubre de 2028: Los sistemas cibernéticos BES de alto impacto y los sistemas de mediano impacto con External Routable Connectivity (ERC) deben cumplir.
1 de octubre de 2030: Todos los demás sistemas cibernéticos BES aplicables con ERC.
CIP-015-2 ya está en marcha. La votación final se aprobó en marzo de 2026, ampliando los requisitos de INSM a los Electronic Access Control and Monitoring Systems (EACMS) y Physical Access Control Systems (PACS) ubicados fuera del ESP. Se espera un cumplimiento ampliado para alrededor de septiembre de 2029.
Consideraciones estratégicas que separan el éxito de la lucha
Línea base vs. firma: Las firmas pasan por alto los ataques de día cero. Las líneas base detectan lo desconocido.
Lo pasivo no es negociable: Cualquier cosa que pueda introducir latencia o requerir agentes en dispositivos OT pone en riesgo la continuidad operativa.
Programa, no proyecto: Vas a gestionar terabytes de telemetría. Trata INSM como una capacidad continua con personas, procesos y tecnología.
La elección del proveedor importa: Busca soluciones diseñadas específicamente para soporte amplio de protocolos OT, detección de anomalías impulsada por IA e informes de cumplimiento sin fricción.
Cómo Shieldworkz hace que NERC CIP-015 & INSM sean sencillos
En Shieldworkz, construimos nuestra plataforma específicamente para entornos como el tuyo. Nuestra solución de Network Detection and Response (NDR) ofrece exactamente lo que exige CIP-015-1, y más.
Monitoreo pasivo y sin agentes en PLC heredados, IoT moderno, SCADA y todo lo intermedio.
Líneas base automatizadas que aprenden el “normal” único de tu instalación en horas, no en semanas.
Detección de anomalías en tiempo real con puntuación de riesgo contextual alineada con IEC 62443 y NERC CIP.
Automatización de cumplimiento integrada: recopilación de evidencia, informes listos para auditoría y protección de datos incorporada.
Servicios de seguridad administrados 24/7 para que tu equipo se mantenga enfocado en las operaciones mientras nosotros manejamos el monitoreo, la búsqueda de amenazas y la respuesta.
Ya sea que operes una subestación de servicios públicos, una planta de manufactura o una instalación de petróleo & gas, Shieldworkz te brinda la cobertura OT más amplia, la implementación más rápida (sin tiempo de inactividad) y perspectivas predictivas que convierten la telemetría en inteligencia accionable. No solo te ayudamos a cumplir con un requisito de cumplimiento: te ayudamos a fortalecer la protección de redes ICS y la defensa de infraestructura crítica a largo plazo.
Prepararse para CIP-015-2 y el camino por delante
La expansión a EACMS y PACS significa que vienen requisitos de visibilidad aún más amplios. ¿La buena noticia? Empezar hoy tu programa INSM con el socio adecuado te coloca por delante de la curva, sin necesidad de costosas sustituciones posteriores.
Conclusión: convierte el cumplimiento en una ventaja competitiva
NERC CIP-015 & Monitoreo interno de seguridad de red (INSM) no es solo otra casilla por marcar: es la evolución que tu entorno OT necesita para mantenerse por delante de las amenazas actuales. Al pasar de una defensa solo perimetral a una visibilidad interna profunda, detectarás anomalías más rápido, responderás con confianza y protegerás los procesos físicos que mantienen en marcha a la sociedad.
¿Listo para pasar de “cumplimiento” a “confianza”?
Descarga gratis nuestro Playbook de cumplimiento de NERC CIP-015-1 en shieldworkz.com o solicita una demostración personalizada hoy mismo. Nuestro equipo mapeará tu entorno, te mostrará la detección de anomalías en vivo en un entorno seguro y te presentará un camino claro hacia la capacidad completa de INSM, sin interrumpir un solo proceso.
Recursos adicionales
Guía de remediación para prevenir este tipo de incidentes de seguridad OT
Guía de remediación para brechas de seguridad de NIS2
Normas de confiabilidad NERC CIP Remediación de brechas posterior a la evaluación
Playbook de remediación de seguridad para PLC (según la guía más reciente de CISA)
Cómo implementar controles IEC 62443
Recibe semanalmente
Recursos y Noticias
Vea cómo nuestras soluciones de seguridad de OT líderes en la industria abordan los desafíos de seguridad críticos
También te puede interesar

SCADA Security: Why Removable Media Is One of the Biggest Attack Vectors in OT Environments

Team Shieldworkz

Navigating Removable Media Compliance: NERC CIP & IEC 62443 for OT/ICS Environments

Team Shieldworkz
Securing the Distributed Grid: Lessons from the First Coordinated Cyberattack on Wind and Solar Infrastructure

Team Shieldworkz
How to Create a Removable Media Security Policy Template

Team Shieldworkz

The Stuxnet USB Attack: Why Removable Media is Still a Threat

Team Shieldworkz
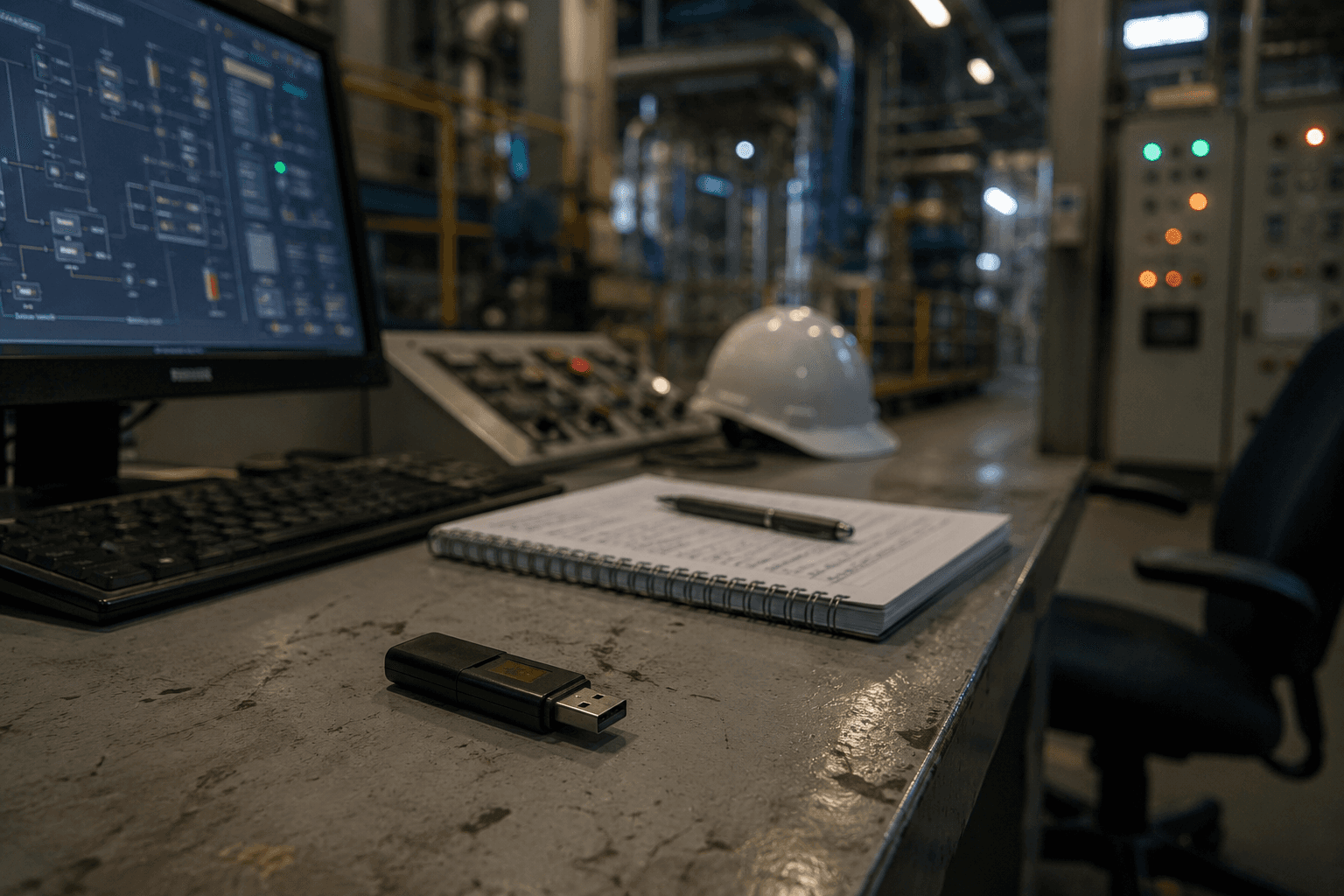
USB Malware Protection: Defending ICS & OT Environments

Team Shieldworkz








