

Prayukth K V
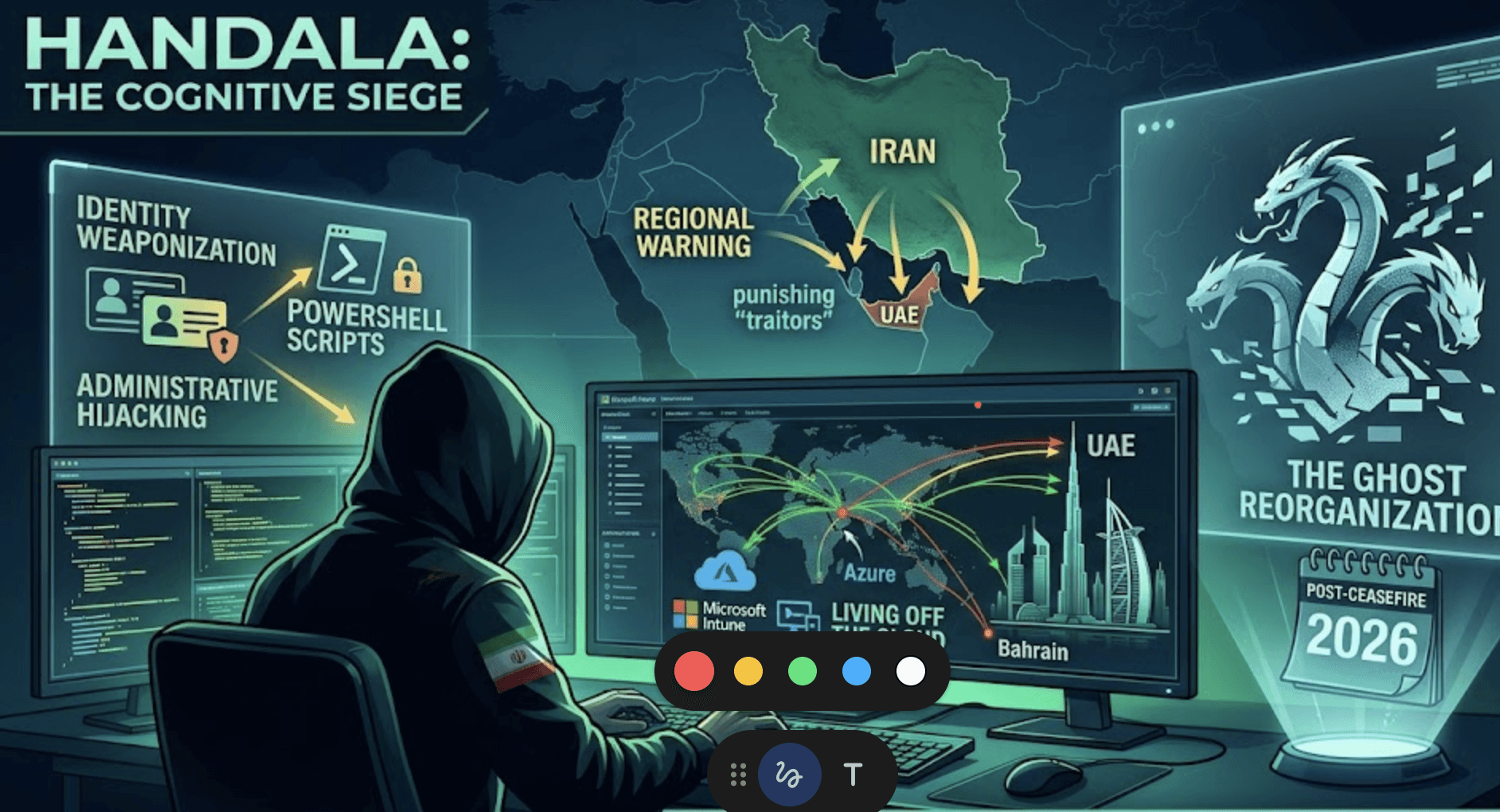
Si hay un actor de amenazas que ha definido el panorama del 1T de 2026, ese es Handala. Desde el incidente de alto impacto de Stryker hasta un número creciente de brechas atribuidas en todo Medio Oriente, el grupo demuestra claramente un impulso operativo sostenido en distintas geografías y eventos. En la publicación de hoy, analizamos a fondo la hoja de ruta proyectada para las próximas operaciones de Handala.
La publicación de hoy también sigue la transición de Handala de operaciones centradas en la interrupción a la guerra centrada en la percepción, donde el impacto psicológico se convierte en el objetivo central y el compromiso técnico en el mecanismo de entrega.
Esta publicación es una continuación de nuestro trabajo de investigación exclusiva sobre Handala. Puedes acceder a publicaciones anteriores aquí,aquí y aquí.
Además, no olvides consultar nuestra publicación de investigación integral sobre el incidente de seguridad OT en la infraestructura de control de inundaciones de San Marcos en Venecia.
Puntos clave
· Handala está pasando de la exfiltración de datos a la interrupción mediante herramientas nativas
· La selección de objetivos se está ampliando en sectores económicos y de infraestructura de Medio Oriente
· Mayor dependencia del compromiso de identidades y de los planos de control en la nube
· Señales tempranas de operaciones psicológicas habilitadas por IA
· El enfoque defensivo debe pasar de la detección de malware al monitoreo de identidades y administradores
Punto de inflexión geopolítico
Aunque las operaciones de Handala a principios de 2026 se centraron principalmente en el preposicionamiento en redes corporativas vinculadas con EE. UU. e Israel (en particular, el borrado medtech de Stryker), sus ataques de abril indican un claro giro hacia objetivos con sede en Medio Oriente.
Handala está yendo más allá de sus objetivos habituales para atacar a vecinos de la región.
Sabotaje económico: al apuntar a entidades ricas en datos y de infraestructura crítica de la región, no solo están robando datos; también están amenazando la estabilidad legal y económica de los centros del Golfo.
En cierto modo, Handala sigue en una postura activa de guerra. El cese al fuego en curso no tiene relevancia para este actor de amenazas. Con los recientes cambios administrativos en Irán, Handala ha ganado más atención y autonomía, y este cambio es claramente visible en las acciones del grupo durante las últimas dos semanas.
Mientras el grupo continúa sus campañas de preposicionamiento en EE. UU. e إسرائيل, Handala ha intensificado sus actividades en Medio Oriente. El objetivo esta vez incluye infraestructura crítica y empresas estadounidenses que operan en la región.
Evolución técnica y táctica: interrupción "nativa"
Handala ha dejado de usar malware personalizado fácil de detectar y se ha orientado hacia el abuso de herramientas nativas.
El manual de Microsoft Intune: en el ataque a Stryker, Handala demostró que podía borrar de forma remota decenas de miles de dispositivos al secuestrar entornos de Microsoft Intune. Handala intentó recientemente vulnerar a una gran entidad estadounidense de petróleo y gas usando una táctica similar, pero el intento fue frustrado por un miembro del equipo de seguridad que dio la alerta.
Qué sigue: en Shieldworkz esperamos que apunten a Proveedores de Servicios Administrados (MSPs), centros de datos y Proveedores de Identidad en la Nube. En lugar de desplegar un "Wiper de Handala", intentarán usar las propias herramientas administrativas de la víctima (como Azure, Intune o JumpCloud) para "desmantelar" la infraestructura. Esto hace que la atribución sea más lenta y la recuperación casi imposible si las "copias de seguridad" también se administran dentro del mismo tenant de nube comprometido.
Shieldworkz ha sabido que Handala está adquiriendo decenas de miles de registros robados cada mes. Este esfuerzo apunta a seguir vulnerando redes desde dentro para usar herramientas administrativas y causar una interrupción mayor
¿Cómo se compara Handala con actores de amenazas conocidos como Lazarus y Sandworm?
El grupo Lazarus trabaja para cumplir objetivos financieros y la interrupción no es un objetivo central
Sandworm ataca sistemas OT para crear un impacto cinético
Los objetivos operativos de Handala incluyen guerra psicológica y en la capa de identidad
Esto convierte a Handala en un actor de amenazas más potente.
Resurrección de los muertos (renacimiento de la persona por IA)
Sin duda, este es el desarrollo más escalofriante tras la muerte de su líder, Panjaki, en marzo. La mayoría de los analistas esperaba un vacío que llevara al colapso gradual de las operaciones. Handala, sin embargo, actuó con rapidez y desplegó su protocolo de "Liderazgo Eterno". En los primeros días, mensajes atribuidos a Panjaki fueron difundidos ampliamente de forma interna por Handala, llamando a la “venganza más allá de las fronteras”. Eso mantuvo alta la motivación de los miembros del grupo durante periodos de intensa actividad y durante los fines de semana. Ahora que el grupo ha seguido adelante, creemos que podría sacar una nueva carta de motivación en los próximos días.
Cuando se operativiza, una resurrección por IA serviría a dos propósitos:
Mantener la moral interna
Fortalecer la propaganda externa y las narrativas de reclutamiento
Esto refleja patrones históricos en los que grupos extremistas han reutilizado imágenes de liderazgo heredadas para mantener su influencia.
Consideramos que el grupo podría experimentar con la reconstrucción de una personalidad generada por IA, aprovechando síntesis de voz y técnicas de deepfake para simular continuidad en el liderazgo.
La resurrección de Panjaki tiene tanto que ver con la motivación como con transmitir que Handala sigue siendo guiado por su antiguo líder, cuyas palabras ahora se vuelven aún más significativas. Este movimiento se basa en el manual que el grupo terrorista Al-Qaeda perfeccionó a principios de los 2000, usando viejos videos de Osama Bin Laden con una superposición de nuevos mensajes en su voz para movilizar a los miembros del grupo.
Pronóstico estratégico de Shieldworkz: los "próximos pasos" de 2026
Fase | Calendario | Objetivo principal | Sector objetivo |
Fase I: actividades regionales | abril - mayo de 2026 | Ataques desestabilizadores contra estados de la región | Bienes raíces, infraestructura crítica, centros de datos, empresas multinacionales y logística |
Fase II: el operativo "Fantasma" | junio - julio de 2026 | PsyOps de "Panjaki" impulsadas por IA y reclutamiento | Medios sociales y tradicionales |
Fase III: asedio a la cadena de suministro | Finales de 2026 | Secuestro de herramientas de administración en la nube | MSPs globales y soporte técnico |
El giro hacia el "asedio cognitivo"
Handala está transitando de un grupo de interrupción a una unidad de guerra psicológica. Su afirmación de haber destruido 6 petabytes de datos, aunque esté exagerada, está diseñada para crear un "asedio cognitivo". Al inundar el espacio informativo con narrativas de amenaza de alto volumen y credibilidad variable, están trabajando para hacer que el mundo digital se sienta inseguro, independientemente del daño técnico real.
Entonces, ¿qué es un asedio cognitivo? Shieldworkz define el “asedio cognitivo” como una presión psicológica sostenida creada mediante interrupción habilitada por ciberataques, amplificación narrativa y fragilidad sistémica percibida.
La conclusión clave es evitar buscar nuevo malware y, en su lugar, buscar credenciales administrativas secuestradas y propaganda deepfake. El próximo movimiento de Handala no es simplemente atacar tus sistemas. En cambio, busca romper tu confianza en esos mismos sistemas que sustentan las operaciones.
Para defenderse de un actor como Handala, hay que entender que opera menos como los "hackers" tradicionales y más como ladrones de identidad convertidos en pirómanos. No solo quieren tus datos; quieren usar tus propias herramientas administrativas para crear un impacto operativo destructivo.
El "asedio cognitivo" de Handala incluye:
Acceso - Compromiso de identidad
Acción - Disrupción con herramientas nativas
Amplificación - narrativa en Telegram/X
Distorsión - afirmaciones exageradas (e incluso falsas)
Persistencia - ciclos repetidos de mensajes
Conclusiones de este “asedio cognitivo”
· La evolución de Handala refleja un cambio de la disrupción pura hacia operaciones de impacto psicológico.
· Las afirmaciones de destrucción de datos a gran escala, estén verificadas o no, cumplen un propósito estratégico: erosionar la confianza en la infraestructura digital.
· Al combinar brechas de datos, mensajes de intimidación y amplificación narrativa, el grupo intenta crear un estado de incertidumbre persistente entre las poblaciones y organizaciones objetivo.
Manual de Handala: TTP clave
Aquí hay un desglose de sus TTP específicas y la realidad "posterior al alto al fuego" en la que estamos entrando. A diferencia de los grupos que usan complejos "Zero-Days", Handala usa "Living off the Land" (LotL) y "Living off the Cloud" para mantenerse invisible.
Armas de identidad (acceso inicial):
Vector: apuntan principalmente a Proveedores de Servicios Administrados (MSPs) y empresas de soporte de TI. Al comprometer a un administrador en un proveedor de servicios, obtienen acceso en "modo dios" a cientos de clientes aguas abajo.
Método: uso extensivo de cuentas VPN comprometidas. A menudo usan VPN comerciales (como Proton o Nord) para ocultar su origen, apareciendo como un hostname estándar "DESKTOP-XXXXXX".
Secuestro administrativo (persistencia y ejecución):
Abuso de Microsoft Intune: este es su movimiento característico de 2026. Secuestran el tenant de Intune o Azure para enviar "scripts de mantenimiento" (en realidad, wipers) a todos los endpoints administrados.
Túneles NetBird: para moverse lateralmente por una red sin activar alertas del firewall, despliegan NetBird, una herramienta de malla zero trust, para crear un túnel privado directamente a sus servidores de Comando y Control (C2).
La estrategia "Quad-Wiper":
Durante la fase final destructiva, a menudo ejecutan cuatro métodos de borrado distintos en paralelo (como un eliminador de MBR, un sobrescritor de sistemas de archivos, un script de PowerShell y un archivo batch). La ejecución paralela mejora la probabilidad de éxito destructivo, incluso si se detectan procesos individuales.
Cómo vigilarlos
Para detectar a Handala, hay que buscar "desviaciones administrativas" en lugar de "firmas de malware".
La alerta de "primera vez": monitorea los inicios de sesión por primera vez desde cuentas administrativas fuera del horario laboral típico, especialmente si provienen de nuevos proveedores de ASN/hosting.
Monitorea cambios en Intune/GPO: configura alertas inmediatas para cualquier nuevo Objeto de Directiva de Grupo (GPO) o Perfil de Configuración de Intune que incluya scripts (normalmente .bat o .ps1).
Revisa NetBird o Tailscale: son herramientas legítimas, pero si tu equipo de TI no las instaló, son una gran señal de alerta. Handala las usa para eludir la supervisión tradicional de VPN.
"Pings" de validación: Handala a menudo prueba credenciales horas antes del ataque. Busca un "inicio de sesión exitoso seguido de cero actividad". Es el atacante verificando que su "llave" funciona antes de prender fuego.
Lista de tareas para los equipos de seguridad
· No busques nuevo malware. Busca el uso indebido de la confianza.
· El modelo de Handala no se basa en exploits novedosos, sino en el control de la identidad, el acceso y los planos administrativos.
· El objetivo ya no es solo la interrupción. Es la negación sistémica de la confianza en las operaciones digitales.
Lista de tareas para los CISOs
Auditar la exposición de identidades privilegiadas en todas las plataformas SaaS
Monitorear el comportamiento administrativo, no solo el malware
Validar la independencia de las copias de seguridad respecto al plano de identidad principal
Establecer monitoreo ciberpsicológico (marca + inteligencia de amenazas)
En el mundo posterior al alto al fuego, Handala está pasando de un "sabotaje ruidoso" a una "infiltración sistémica de bajo ruido". Ya no solo buscan aparecer en los titulares; buscan adueñarse de las "tuberías" de internet para poder apagarlas en cualquier momento.
Recursos adicionales
Lista de verificación de remediación de seguridad PLC
Lista de verificación base de seguridad OT
Recibe semanalmente
Recursos y Noticias
Vea cómo nuestras soluciones de seguridad de OT líderes en la industria abordan los desafíos de seguridad críticos
También te puede interesar
How to Create a Removable Media Security Policy Template

Team Shieldworkz

The Stuxnet USB Attack: Why Removable Media is Still a Threat

Team Shieldworkz
USB Malware Protection: Defending ICS & OT Environments

Team Shieldworkz

USB Device Control Policy Guide for Industrial Networks

Team Shieldworkz

15 Removable Media Security Best Practices for OT and ICS Environments

Team Shieldworkz

Sistemas de defensa de China expuestos a Internet: lecciones sobre el fracaso cibernético moderno

Prayukth K V








