


Team Shieldworkz
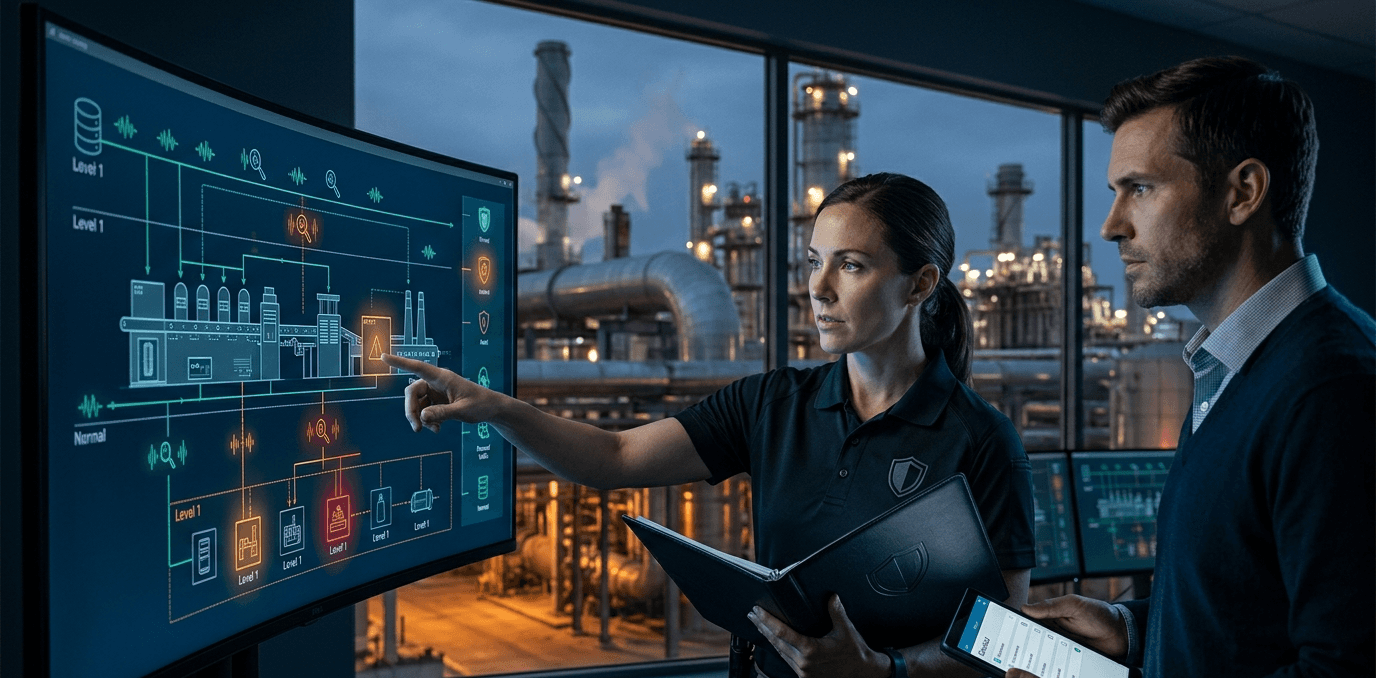
If you manage an industrial facility today, you already know that the traditional "air gap" is no longer a reliable standalone defense. Your Operational Technology (OT) and Industrial Control Systems (ICS) are increasingly connected to enterprise networks, the cloud, and Industrial IoT (IIoT) devices. While this connectivity drives massive leaps in efficiency and predictive maintenance, it also exposes legacy machinery to a hyper-connected threat landscape.
Whether you are a plant manager, an OT engineer, or a CISO, protecting critical infrastructure-from power grids to water treatment plants and manufacturing floors-is no longer just about keeping unauthorized users off the corporate Wi-Fi. It is about ensuring that a digital glitch or a targeted cyberattack does not result in a catastrophic physical event, environmental disaster, or prolonged operational downtime.
This is where the IEC 62443 standard comes in. It is the globally recognized benchmark for securing industrial automation and control systems (IACS). But reading through international standards can often feel like translating a foreign language.
In this comprehensive guide, we are going to break down the core framework of IEC 62443, demystify the four critical Security Levels (SL1-SL4), and provide you with actionable, step-by-step tactics to defend your critical infrastructure.
Before we move forward, don’t forget to check out our previous blog post on “The attack that failed: Lessons from Sweden’s near-miss OT incident” here
The Unique Landscape of OT Security: Why IT Rules Don't Apply
Before we dive into security levels, we need to address a common misconception: you cannot simply copy and paste your IT security policies onto your OT environment.
In traditional Information Technology (IT), the primary goal is protecting data confidentiality. If a bank detects a breach, the system might automatically shut down servers to protect sensitive customer data.
In Operational Technology (OT), the primary goals are availability and safety. If a digital system running a chemical plant's cooling mechanism detects an anomaly, simply shutting it down could cause an explosion. OT systems operate in real-time (often measured in milliseconds). A 100-millisecond delay caused by a heavy network scan or encryption process might mean a robotic arm fails to stop in time to prevent an accident.
Furthermore, IT hardware is typically replaced every three to five years, allowing for constant software patching. Industrial assets-like turbines, pumps, and programmable logic controllers (PLCs)-are designed to last 20 to 30 years. They often run on legacy operating systems that require compensating measures instead of direct hardening or patching.
Here is a quick breakdown of how IT and OT priorities differ:
Feature | IT Security (e.g., ISO 27001) | OT Security (IEC 62443) |
Primary Risk | Identity theft, data loss, financial loss. | Physical damage, environmental disaster, loss of life. |
Core Priority | Confidentiality (Privacy of data). | Availability & Safety (Keep the process running safely). |
Performance | Non-time-critical (high latency is annoying but acceptable). | Real-Time / Deterministic (delays can cause physical accidents). |
Asset Lifecycle | 3-5 years (Laptops, enterprise servers). | 15-30 years (Turbines, PLCs, SCADA systems). |
Patching Strategy | Frequent, often automated updates. | Strictly scheduled, rarely updated, relies heavily on compensating controls. |
Because of these extreme differences, a dedicated framework like IEC 62443 is essential. It provides a shared language for IT and OT teams to collaborate securely without compromising the safety and reliability of the plant floor.
The Core of IEC 62443: Zones, Conduits, and Defense-in-Depth
Before assigning security levels, you must understand how IEC 62443 structures a network. The standard relies on a segmentation model known as Zones and Conduits.
If an attacker breaches a flat, unsegmented network, they can easily move laterally from a compromised billing laptop straight to the engineering workstation controlling a physical valve. The IEC 62443 framework limits this lateral movement through strict logical isolation.
Zones: These are logical or physical groupings of assets (like PLCs, HMIs, or sensors) that share similar security requirements. By grouping these assets, you create a defined perimeter. If a threat compromises one zone, the segmentation keeps the threat contained, protecting the rest of the facility.
Conduits: These are the controlled communication pathways between zones. A conduit is typically governed by a boundary device, such as an industrial firewall or a unidirectional gateway.
Practical Example: Imagine a water treatment facility. You might create a "General Operations Zone" for operator workstations (requiring moderate security) and a "Chemical Dosing Zone" for the PLCs that manage chlorine levels (requiring maximum security). The conduit between them would feature a firewall configured to allow only specific read-only polling queries. Operators can monitor the chlorine levels on their screens, but if a compromised workstation attempts to send a configuration change to dump excess chlorine, the conduit explicitly drops and logs the traffic.
This segmentation is the foundation of Defense-in-Depth-deploying multiple, overlapping layers of technical, physical, and process controls so that if one fails, others are standing by to neutralize the threat.
Demystifying IEC 62443 Security Levels (SL1 - SL4)
The IEC 62443 Security Levels provide a risk-based roadmap for industrial resilience. They measure the necessary robustness of an IACS to withstand cyber threats, scaling from casual mistakes to highly sophisticated, well-funded attacks.
You do not need to apply the highest security level to every single machine. Instead, you apply the appropriate level to specific zones based on the actual risk they carry. Let's break down the four levels and what they mean for your plant floor.
Security Level 1 (SL1): Protection Against Casual or Accidental Misuse
SL1 is your baseline. It is not designed to stop a dedicated, malicious actor; rather, it protects against unintentional human errors, careless handling of data, or non-malicious actions.
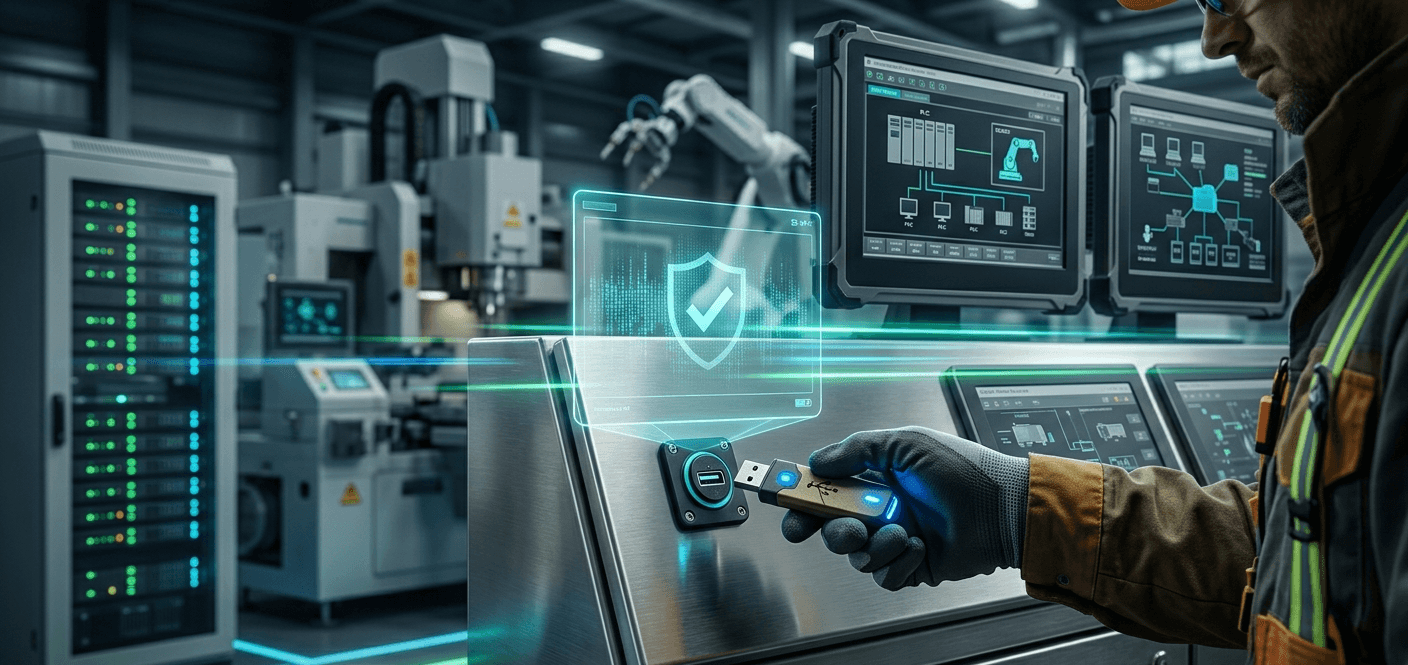
The Threat: An employee accidentally plugging an infected USB drive into an engineering workstation, emailing sensitive configurations to the wrong person, or unintentionally altering a machine's set-point.
Core Requirements:
Basic authentication (unique usernames and passwords).
Fundamental network segmentation (separating the enterprise IT network from the OT network).
Disabling unused ports and services on industrial devices.
Basic physical access restrictions.
Actionable Tactic for SL1: Eliminate shared or default passwords (e.g., "admin/admin") on all factory floor devices immediately. Ensure that every operator has a unique login, making actions traceable.
Security Level 2 (SL2): Protection Against Simple Intentional Attacks
SL2 represents the standard protection level required for most standard industrial zones. It defends against intentional violations by attackers who have low motivation, limited resources, and use generic, widely available hacking tools.
The Threat: Script kiddies, opportunistic ransomware, password guessing, or basic phishing attacks targeting operator workstations.
Core Requirements:
Role-Based Access Control (RBAC): Users only have access to the specific zones and functions required for their jobs.
Secure Remote Access: Implementation of Virtual Private Networks (VPNs) with strong session management.
Event Logging: Systems must generate timestamped audit records for all security-relevant events.
Automated Session Locks: Systems must lock out users after a set period of inactivity to prevent physical hijacking of a workstation.
Actionable Tactic for SL2: Implement a "Jump Server" in a Demilitarized Zone (DMZ) for all remote access. Never allow an engineer or third-party vendor to connect directly from the public internet into the OT environment. They must connect to the jump server first, authenticate, and then access the specific plant system.
Security Level 3 (SL3): Protection Against Sophisticated Intentional Attacks
When we enter SL3, we are looking at critical infrastructure systems where a breach could cause significant financial loss, operational downtime, or safety hazards. This level protects against skilled, highly motivated attackers with IACS-specific knowledge.
The Threat: Targeted ransomware gangs, customized malware designed specifically for OT protocols, or skilled hackers utilizing multi-vector network intrusions.
Core Requirements:
Strong Authentication: Multi-Factor Authentication (MFA) is a critical compensating control and strong recommendation for all remote access under SL3, and highly recommended for local administrative access.
Active Intrusion Detection: Deployment of specialized OT network monitoring tools that understand industrial protocols (like Modbus or PROFINET) to detect anomalous behavior.
Strict Least Privilege Enforcement: Access policies where trust is never assumed, even inside the network.
Encrypted Data Transfer: Securing data in transit to prevent "Man-in-the-Middle" attacks from altering sensor readings, where technically feasible without impacting latency.
Actionable Tactic for SL3: Deploy network test access points (TAPs) to passively monitor your OT network traffic. Passive monitoring allows you to detect customized malware and anomalous commands without adding latency or risking disruption to real-time deterministic networks.
Security Level 4 (SL4): Protection Against Advanced / Nation-State Attacks
SL4 is designed for environments facing the most severe threat landscapes, such as critical power generation or major oil and gas pipelines. This defends against adversaries with extensive resources, high motivation, and deep, specialized knowledge of your specific control systems.
The Threat: State-sponsored cyber warfare, advanced persistent threats (APTs), zero-day exploits, and coordinated attacks aimed at causing mass physical destruction or prolonged societal disruption.
Core Requirements:
Hardware-Based Security: Utilizing Trusted Platform Modules (TPM) or Hardware Security Modules (HSM) for tamper-resistant, hardware-level authentication where possible.
Dual Authorization: Critical actions (like opening a safety valve or shutting down a primary cooling system) require two separate authorized individuals to approve the command simultaneously.
Advanced Forensic Logging: Full traffic capture and packet analysis stored in secure repositories.
Continuous Anomaly Detection: Near-real-time behavioral analysis of all network traffic.
Actionable Tactic for SL4: For ultra-critical zones that must send data outward (e.g., sending performance data to a predictive maintenance cloud), consider replacing standard firewalls with Unidirectional Gateways (Data Diodes). These physical hardware devices only allow data to flow out, establishing a physical barrier against inbound malicious commands.
The SL Lifecycle: Target, Capability, and Achieved Levels
When implementing these levels, it is crucial to understand that a "Security Level" is not a single static label. While specific parts of the IEC 62443 standard (like 62443-3-3) focus heavily on establishing system requirements, the broader framework and practical ISA training methodologies rely on three distinct metrics to help you assess your security posture:
SL-T (Target Security Level): This is the desired level of security you need for a specific zone, determined by your initial risk assessment. (e.g., "Based on the risk profile, our chemical mixing zone requires an SL-T of 3.")
SL-C (Capability Security Level): This is the maximum level of security that a specific device or system is technically capable of providing if configured optimally. (e.g., "The new PLC we purchased has built-in features that give it an SL-C of 3.")
SL-A (Achieved Security Level): This serves as a practical measure of your field security-the actual, verified level currently operating on your floor. (e.g., "Even though the PLC has an SL-C of 3, we haven't enabled the advanced authentication features yet, so our operational SL-A is only 1.")
Your operational goal is to align these metrics over time so that your Achieved level meets your Target level (SL-A ≥ SL-T).
The Role of Compensating Controls
What happens when your SL-T is 3, but you are running a 20-year-old turbine controller that maxes out at an SL-C of 1? You cannot easily rip out the turbine.
Instead, you use Compensating Controls. Because the legacy asset cannot defend itself natively, you build a protective perimeter around it. You place the vulnerable asset in a strictly isolated zone, apply deep protocol filtering at the conduit, and use virtual patching at the firewall level. These compensating measures elevate the overall Achieved security of the zone without touching the fragile legacy equipment.
A Practical Risk-Based Implementation Strategy
You cannot secure everything at once without bringing production to a grinding halt. Implementing IEC 62443 requires a pragmatic, risk-based approach. Here is how we at Shieldworkz recommend structuring your implementation workflow:
Step 1: Assemble a Cross-Functional Team
Cybersecurity is no longer just an IT problem. Your assessment team must include IT security specialists, OT engineers, production managers, and subject matter experts who understand the physical realities of the machinery.
Step 2: Define the System Under Consideration (SuC)
Clearly map out the boundaries of the system you are analyzing. Maintain a comprehensive asset inventory that includes hardware, software, firmware versions, and the physical location of the assets.
Step 3: Logically Isolate and Segment (Define Zones and Conduits)
Group your inventoried assets into logical zones based on their criticality and function. Document every single communication path (conduit) between these zones. If a communication path is not strictly necessary for production, eliminate it.
Step 4: Conduct a Worst-Case Scenario Risk Evaluation
For each zone, evaluate the likelihood and impact of a threat. Look beyond financial data loss. Ask: What happens to human safety if this PLC is compromised? What is the environmental impact if this valve is forced open?
Step 5: Assign Target Security Levels (SL-T)
Based on the worst-case scenarios, assign an SL target for every zone and conduit.
Step 6: Deploy Mitigation and Compensating Controls
Begin applying the core requirements for your target levels. Deploy dedicated industrial firewalls, tighten remote access protocols, and set up centralized OT network monitoring.
Your IEC 62443 Actionable Checklist
To help you move from theory to practice, we have categorized common vulnerabilities by their urgency. Use this checklist to build your immediate and long-term OT security roadmaps.
Critical Risk Items (Address within 24-72 Hours)
These are vulnerabilities that threaten the immediate safe operation of your plant.
[ ] Eliminate Flat Networks: Ensure there is a hardened firewall strictly separating the corporate IT network from the OT/SCADA network.
[ ] Kill Direct Remote Access: Disable all direct remote connections (like consumer-grade remote desktop applications or unmanaged RDP) into OT assets. Route all external access through a secure Jump Server.
[ ] Enforce Strong Authentication: Mandate stringent authentication (such as MFA) for any remote session entering the OT environment.
[ ] Remove Default Credentials: Audit all PLCs, HMIs, and network switches to ensure factory default passwords have been changed to strong, unique credentials.
Medium Risk Items (Address within 3-6 Months)
These issues weaken your overall resilience and visibility.
[ ] Complete Your Asset Inventory: Build a dynamic inventory that tracks not just hardware, but firmware versions, component owners, and criticality levels.
[ ] Establish Virtual Patching: For unpatchable legacy systems, configure Intrusion Prevention Systems (IPS) to block known exploits at the network boundary.
[ ] Deploy Passive Monitoring: Implement an industrial-grade Intrusion Detection System (IDS) to monitor network traffic for anomalous behavior without impacting latency.
[ ] Formalize Change Management: Ensure no firewall rule or PLC logic can be changed without a formal review, approval, and documented rollback procedure.
Low Risk Items (Ongoing Maintenance)
These actions ensure your security posture doesn't degrade over time.
[ ] Routine Log Reviews: Schedule weekly or monthly reviews of access logs and SIEM alerts to identify slow-moving threats.
[ ] OT-Specific Training: Conduct regular cybersecurity awareness training tailored specifically for plant floor operators and engineers (e.g., recognizing specialized phishing attempts, safe USB handling).
[ ] Backup Restoration Drills: Do not just back up your data-regularly test your ability to restore critical SCADA configurations and PLC logic from those backups in a simulated disaster scenario.
[ ] Update Documentation: Routinely review your network diagrams to ensure they accurately reflect the actual physical and logical configuration of your plant floor.
Securing critical infrastructure is not a one-time project; it is a continuous lifecycle of assessment, implementation, and monitoring. The IEC 62443 standard provides a robust, globally recognized framework to ensure that your industrial environments remain safe, resilient, and operational in the face of an evolving threat landscape.
By shifting away from traditional IT perimeters and adopting an OT-centric approach-utilizing Zones and Conduits, targeted Security Levels (SL1-SL4), and strict Compensating Controls-you can dramatically reduce your exposure to devastating cyber-physical attacks.
Ready to defend your critical infrastructure? At Shieldworkz, we specialize in translating complex frameworks into operational reality. We understand that security must never compromise plant performance.
Take the next step in your OT security journey today. Request a Demo with our Shieldworkz OT security experts to see how our solutions can map your network, identify vulnerabilities, and secure your plant floor without disrupting a single second of production.
Additional resources
Comprehensive Guide to Network Detection and Response NDR in 2026 here
A downloadable report on the Stryker cyber incident here
Remediation Guides here
OT Security Best Practices and Risk Assessment Guidance here
IEC 62443-based OT/ICS risk assessment checklist for the food and beverage manufacturing sector here
Get Weekly
Resources & News
See How Our Industry-Leading OT Security Solutions Address Critical Security Challenges
You may also like
10 Essential Requirements to Include in an OT Threat Detection RFP

Team Shieldworkz
Best USB Device Control Software for OT Networks

Team Shieldworkz

The USB drive that could shut down a refinery

Team Shieldworkz

The Ultimate Guide to Zero Trust Security for Industrial Control Systems

Team Shieldworkz

SCADA Security: Why Removable Media Is One of the Biggest Attack Vectors in OT Environments

Team Shieldworkz

Navigating Removable Media Compliance: NERC CIP & IEC 62443 for OT/ICS Environments

Team Shieldworkz








