


Prayukth K V
The targeting of a Swedish thermal power plant in the spring of 2025 that was recently confirmed by Minister of Civil Defense Carl-Oskar Bohlin marks a significant escalation in the hybrid warfare being waged against European energy infrastructure. While everyone talks about cyberattacks that succeeded, it is important to talk extensively about cyberattacks that were defeated. There are lessons lessons in both failure and success and therefore it is essential to understand how this cyberattack played out and how it was stopped in its tracks.
As we have seen over the last two years, this is not an isolated incident. Russian threat actors have been stress testing European critical infrastructure across countries. In fact this attack was a precursor to a more destructive, large-scale campaign launched against Poland in December 2025.
It is heartening to note that neither of these attacks succeeded.
In today’s post, we do a deep dive into the attack on the Swedish thermal power plant, examine various dimensions and linkages associated with this attack and outline the steps to prevent such attacks.
As always, before moving forward, don’t forget to check out our previous blog post on NERC CIP compliance here.
Background
Sweden’s thermal power sector primarily focuses on sustainable combined heat and power (CHP). Major plants use biomass to provide district heating and electricity across the country. Key facilities include the Värtaverket biofuel plant in Stockholm and the Rya CHP plant in Gothenburg, while Karlshamnsverket serves as a vital oil-fired reserve plant. Sweden is aggressively converting older coal/oil plants to biomass and waste-derived fuels to achieve its carbon neutrality goals.
Beginning early 2025, Shieldworkz noticed a spike in reconnaissance attacks targeting European countries. This followed a lull that lasted nearly eight months where things turned eerily quiet in European cyberspace. The rising recon attacks broke that pattern and targeted attacks on renewable energy generation and associated infrastructure began to rise. Someone (we all know who that is) didn’t like or want Europe to move faster towards renewable power generation.
The incident: A shift from nuisance to sabotage
Globally, for years, the energy sector has primarily dealt with disruptive but largely superficial Distributed Denial of Service (DDoS) attacks. Such attacks often follow a period of extended reconnaissance.
This incident represents a structural shift in adversary intent and capability. A pro-Russian hacktivist group, acting as a proxy for Russian intelligence, bypassed the IT perimeter and directly engaged the Operational Technology (OT) infrastructure. Sustained reconnaissance activity enabled the threat actor to map the OT environment and design a targeted intrusion strategy.
Target: A major thermal power plant in western Sweden.
Timeline: Spring 2025.
Outcome: Thwarted by a "built-in security system" before any kinetic or other form of damage occurred.
What went wrong: The vulnerable edge
While the Swedish plant’s defenses held, the "anatomy" of the attempt revealed a more dangerous trend. Attackers are no longer just looking to exfiltrate data or stick around for a while or even sell the access they gained. They were looking to manipulate the grid. This attack may have been one of the earliest attacks that enabled Russian threat actors to create a playbook for attacks on European critical infrastructure.
The vector: Attackers targeted unpatched edge devices and exposed remote access points, a strategy they perfected months later in Poland.
The intent: The goal was to create a "Loss of Control" allowing a hostile actor to shut down turbines or corrupt the data flowing to operators, creating a dangerous "blind spot."
The threat actor: The intelligence proxy
Minister Bohlin’s attribution points to a pro-Russian hacktivist group with clear ties to Russian intelligence services (likely Russia's GRU the Main Intelligence Directorate, specifically unit 74455).
As per Shieldworkz research, this aligns with the behavior of groups like Static Tundra (Berserk Bear) or Sandworm, who often use "hacktivist" fronts to mask state-sponsored operations and maintain plausible deniability.
We feel that this attack was used to train new members of Sandworm on carrying out attacks on OT infrastructure
Damage: A near miss
Unlike the attack on Poland's grid in December 2025, which saw over 30 sites hit with wiper malware, the Swedish incident resulted in no serious consequences. The attack was detected and acted upon in time. The plant's "built-in security" (likely physical fail-safes or hard-coded safety logic) prevented the digital intrusion from escalating into a kinetic failure.
Patterns of aggression: The EU OT threat landscape
This incident is a single data point in a broader, aggressive campaign targeting the EU's energy stability.
Country | Incident profile | Key difference |
Sweden | Spring 2025 attempt on a thermal plant. | Thwarted by hard-coded OT safety mechanisms. |
Norway/Denmark | Multiple "similar incidents" confirmed by Bohlin. | Often characterized by long-term reconnaissance and probing of edge devices. |
Poland | December 2025 massive strikeon 30+ sites. | Used DynoWiper malware to destroy RTU firmware and HMI data. |
Preventing such attacks on OT in the future
Securing the grid is no longer just about guarding the "castle" (central power plants) or even the moat. Instead it’s about securing the entire "neighbourhood" (distributed wind and solar sites).
Drawing from the lessons of the Swedish and Polish attacks, here are 10 key steps critical infrastructure operators can take to harden their OT environment against state-sponsored sabotage.
1. Execute a complete asset discovery (know the unknowns)
You cannot protect what you cannot enumerate. Distributed sites often have "unaccounted" assets primarily old RTUs or communication modules forgotten after a project’s completion.
Action: Use passive discovery NDR tools such as Shieldworkz to catalog every PLC, HMI, and relay. Map their firmware versions and communication protocols.
2. Enforce strict network segmentation
Stop lateral movement. If an attacker breaches a VPN in a wind farm, they should not be able to reach the neighboring solar site or the main control center.
Action: Implement Zones and Conduits (per ISA/IEC 62443) and assign zone owners. Isolate OT process networks from the business IT network with a hardened Industrial DMZ.
3. Implement Multi-Factor Authentication (MFA) everywhere
The Polish attack proved that default credentials and stolen passwords are the primary keys for entry.
Action: Enforce MFA for all remote access. If a legacy device doesn't support MFA, place it behind a secure gateway or Jump Host that does.
4. Hardware Root-of-Trust and Secure Boot
Malware like DynoWiper succeed by overwriting the firmware. If the hardware can't verify the code it's running, it's a brick waiting to happen.
Action: Transition to hardware with Secure Boot capabilities. Use Trusted Platform Modules (TPM) to ensure only digitally signed, authorized firmware can execute.
5. Disable unused ports and default accounts (audit privileges)
"Shadow" access points are a gift to threat actors like Static Tundra.
Action: Close all unused physical and logical ports (FTP, Telnet, HTTP). Change every factory-set password on day one of deployment.
6. OT-Specific anomaly detection
IT security looks for stolen data; OT security must look for "impossible" physical commands or any deviations from baseline traffic patterns.
Action: Deploy Network Detection and Response (NDR) tools that understand industrial protocols (Modbus, DNP3, IEC 60870-5-104). Alert on unusual commands, like a mass "reboot" signal sent to 50 RTUs simultaneously.
7. Firmware integrity and "anti-rollback" protections
Attackers often try to "downgrade" a device to an older, vulnerable firmware version.
Action: Enable anti-rollback mechanisms in your update pipeline. This ensures a device cannot be forced back to a version with known security gaps.
8. Establish an "offline" recovery baseline
If a wiper hits, your "View" is gone. You need to be able to rebuild from scratch without an internet connection.
Action: Maintain verified, offline backups of all PLC logic, HMI configurations, and relay settings. Practice "cold-start" recovery drills annually.
9. Supply chain rigor (The "Trusted Vendor" loop)
The Swedish incident highlights that proxies often target the tools or vendors you trust most.
Action: Audit your vendors' security practices. Ensure that maintenance laptops brought on-site by third parties are scanned in a "clean room" before connecting to your network.
10. Align with NIS2 and NERC CIP Playbooks
Regulatory compliance isn't just paperwork; it's a defensive baseline.
Action: Use Shieldworkz Regulatory Playbooks and Remediation Guides to automate compliance reporting and ensure you are meeting the latest EU mandates for incident reporting and risk management.
The takeaway
The Swedish attack was essentially a "probe." Just like Russian Air Force aircraft that constantly test the state of European Air Defense readiness, Russian units were checking the access paths and defense mechanisms available to figure out ways to outflank them.
By testing the defenses of a single plant in the spring, the threat actor gathered intelligence on European critical infrastructure OT security postures. This intelligence was used to refine the automated destructive tools seen in the massive December 2025 Polish campaign. The tools and tactics of Russian threat actors are evolving and so should the defenses deployed to prevent such actors from succeeding.
The lesson for grid operators is clear: Operational Technology is the new front line. We must move beyond IT-style security band aid like fragmented responses and implement a comprehensive and integrated response spread across detection and response. If you haven't audited your firmware integrity and completed asset enumeration lately, you are operating on borrowed time.
For detailed strategies on defending these critical assets, review the latest OT security benchmarks at Shieldworkz.
Additional resources
Comprehensive Guide to Network Detection and Response NDR in 2026 here
A downloadable report on the Stryker cyber incident here
Remediation Guides here
OT Security Best Practices and Risk Assessment Guidance here
IEC 62443-based OT/ICS risk assessment checklist for the food and beverage manufacturing sector here
Get Weekly
Resources & News
You may also like

Top 15 Challenges in CPS Protection and How OT Teams Can Address Them

Team Shieldworkz

Demystifying IEC 62443 Security Levels SL1-SL4 for Critical Infrastructure Defense

Team Shieldworkz

NERC CIP-015 & Internal Network Security Monitoring (INSM)

Team Shieldworkz
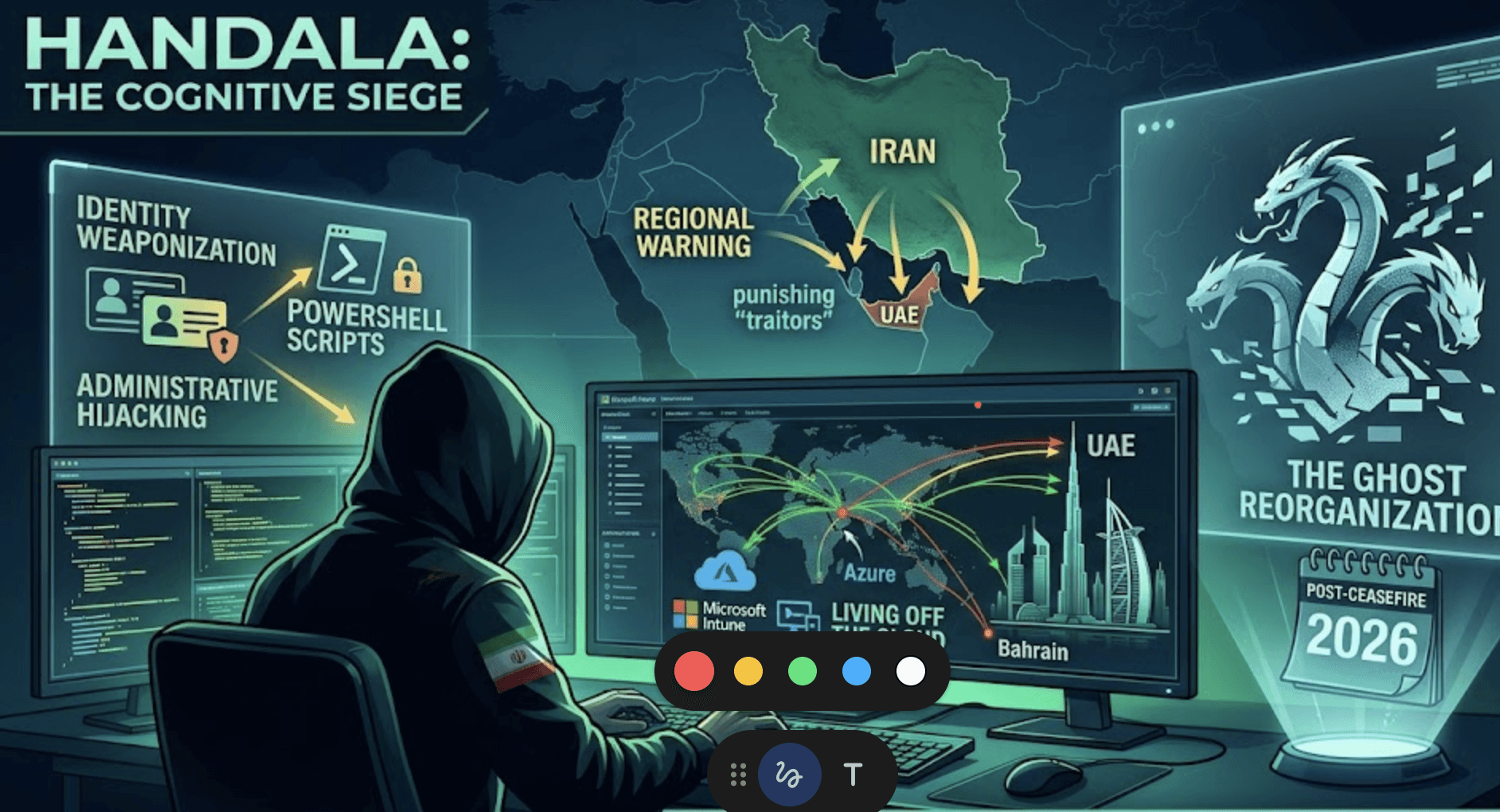
Handala’s next gambit: From "hack-and-leak" to "cognitive siege"

Prayukth K V

HMI vulnerabilities in Venice: A deep dive into the San Marco pump incident

Prayukth K V
East-West Traffic Monitoring in OT Meeting NERC CIP-015 Requirements

Team Shieldworkz







