Data Centers (industrial OT environments) - OT, ICS & IIoT Security by Shieldworkz
How Shieldworkz secures data center OT environments
Shieldworkz applies a layered, engineering-first program that protects uptime while reducing attack surface:
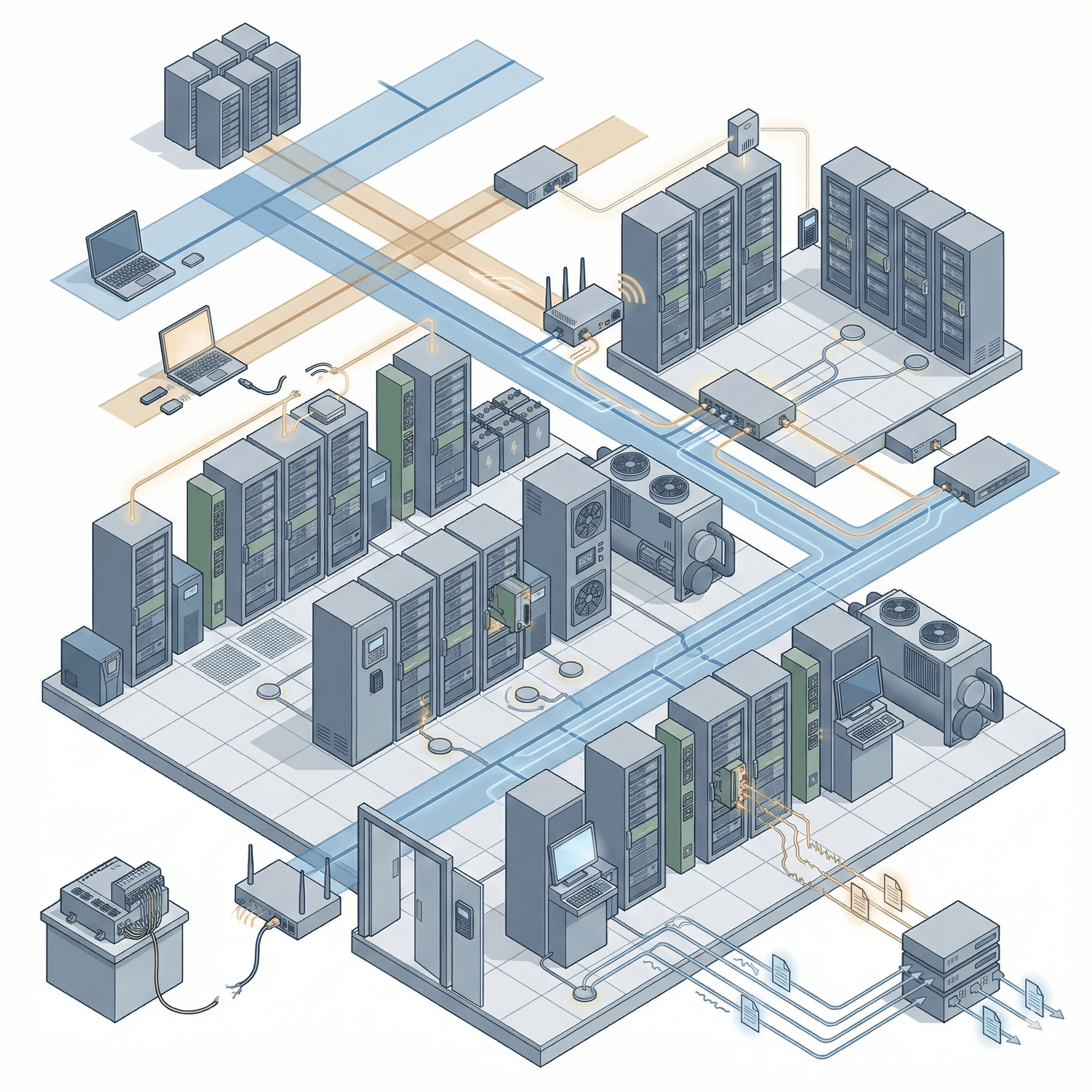
1. Production-safe discovery & comprehensive inventory
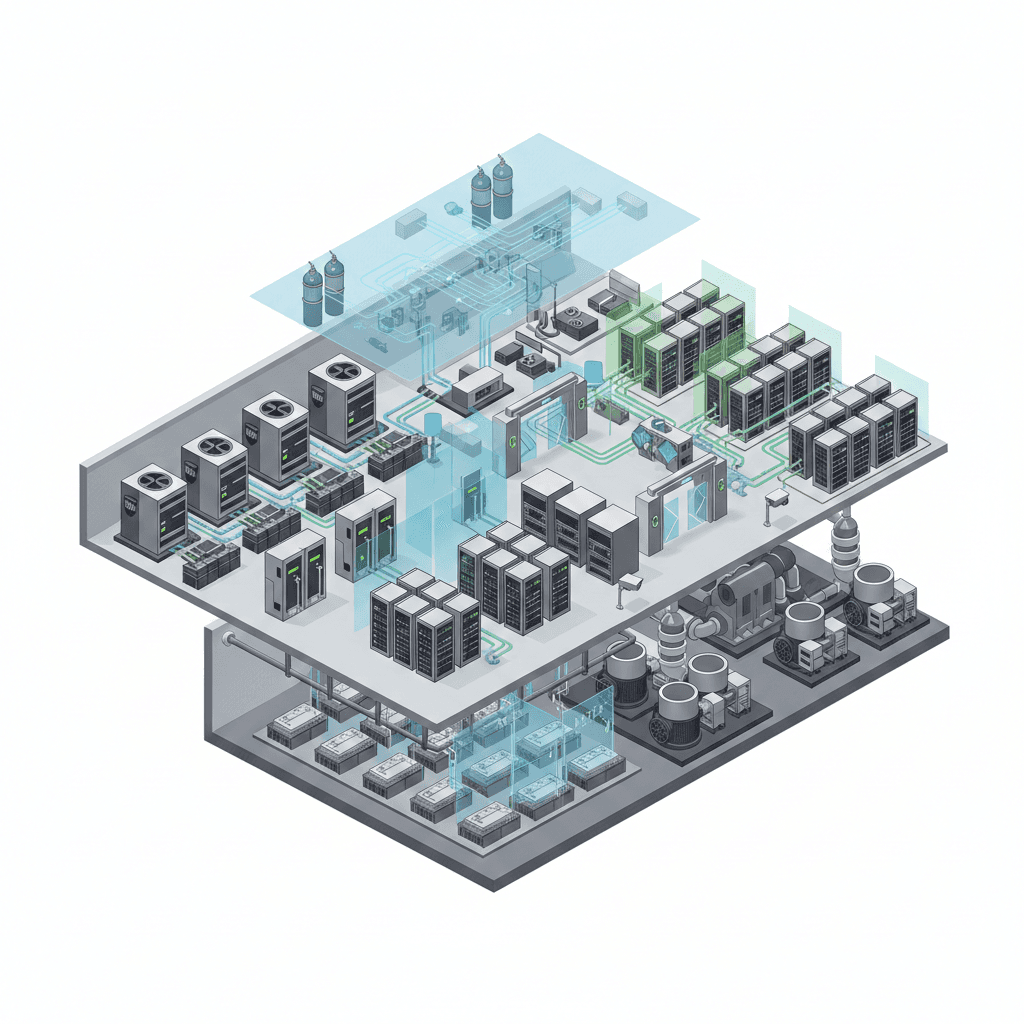
We discover and fingerprint PDUs, UPS, battery management, CRACs, chillers, BMS, fire suppression controllers, generators, rack sensors and vendor consoles using passive traffic capture and calibrated active techniques that avoid disturbing control loops. Every device is mapped to racks, zones, redundancy domains and service owners.
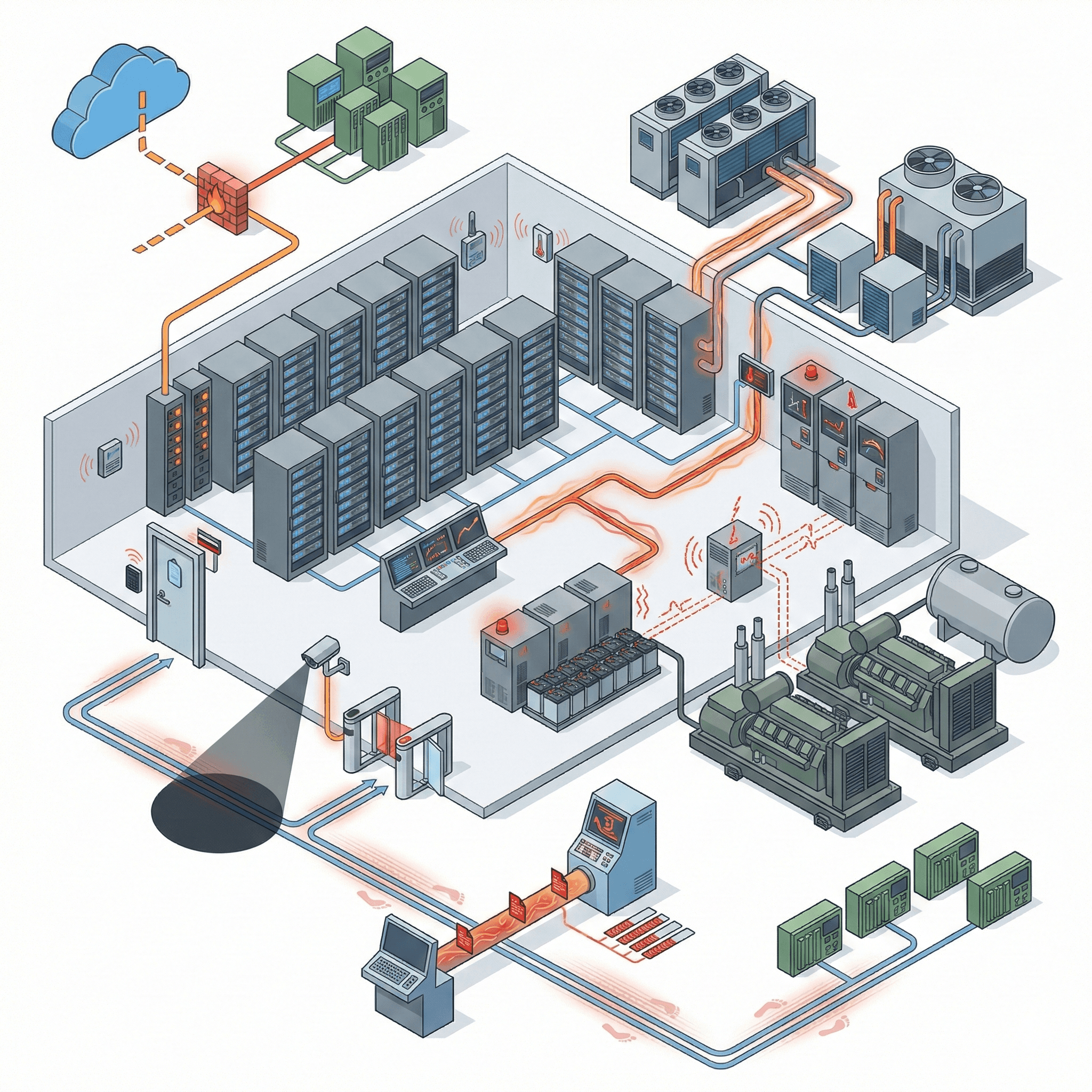
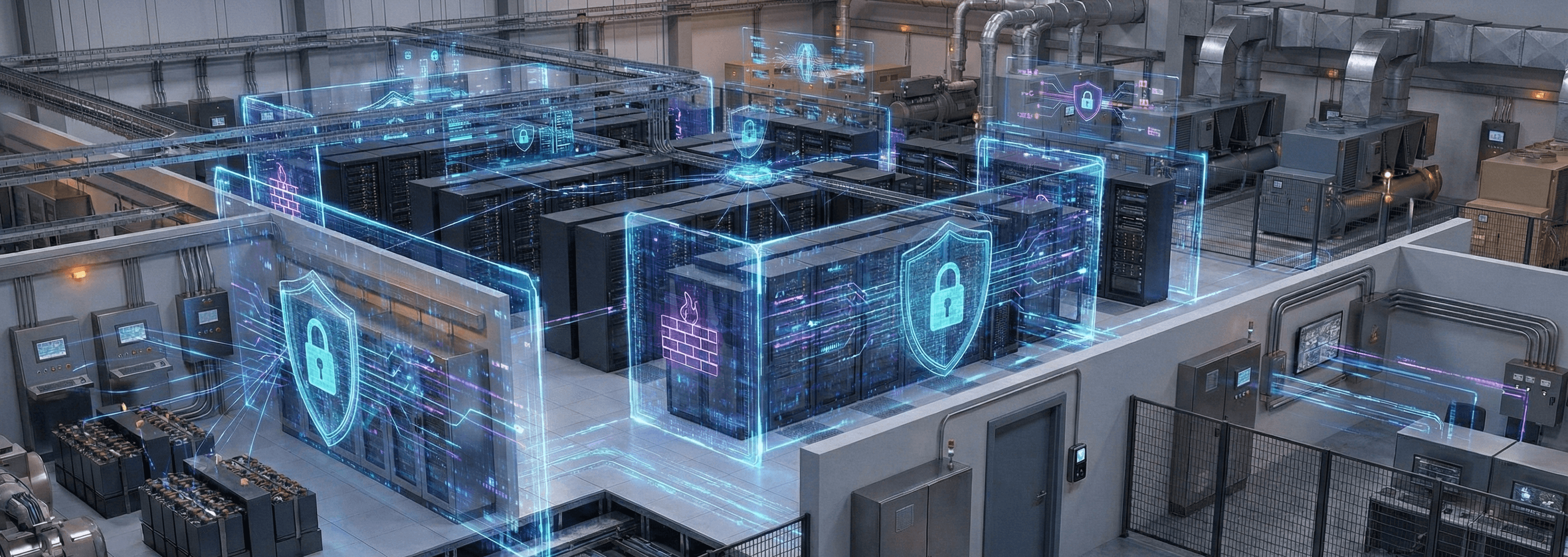
2. Asset concealment & logical cloaking
Where appropriate, Shieldworkz applies asset concealment and invisibility controls that make critical OT systems invisible to unauthorized scans and reconnaissance-reducing the available attack surface without changing operational topology.
3. Protocol-aware behavioral baselining
We build semantic baselines of control commands, telemetry cadence and maintenance patterns. This lets teams detect meaningful deviations-unauthorized breaker operations, out-of-profile CRAC cycles, or anomalous UPS switching-while keeping false positives low.
4. Micro-segmentation & safe enforcement
Shieldworkz designs micro-segmentation aligned to redundancy zones and failover paths. Segmentation rules are validated against control-plane timing and tested in staging to ensure no interruption to redundancy or N+1 behavior.
5. Secure remote access & vendor governance
All third-party sessions are brokered with least-privilege, time-bound credentials, multi-factor authentication and session recording. Shieldworkz provides just-in-time access, instant revocation and audit trails for every maintenance session.
6. OT-aware detection & OT-MDR
Our detection engines are tuned for Modbus, SNMP, BACnet, OPC UA and vendor stacks used in data center infrastructure. Shieldworkz offers 24/7 OT-MDR: analysts experienced in power and HVAC controls deliver contextual triage, production-safe containment, and industrial forensics.
7. Immutable logging & forensic evidence
Events are preserved in tamper-resistant, auditable formats to support regulator engagement, SLA dispute resolution and insurance claims. Forensic exports include time-synced telemetry, command logs and recorded maintenance sessions.
Platform capabilities - Engineered for resilient facilities
Shieldworkz platform features built for data center operations:
Passive, non-disruptive asset discovery across segmented and intermittent management links
Deep protocol decoding (Modbus, SNMP, BACnet, OPC UA, vendor APIs) with semantic control analysis
Time-series correlation linking telemetry, network events and maintenance sessions
Asset concealment (logical cloaking) for critical OT endpoints to prevent reconnaissance
Automated segmentation design and enforcement validation mapped to redundancy and failover domains
Secure remote-access brokering with MFA, JIT credentials and session recording
Firmware and configuration monitoring for PDUs, UPS, BMS and CRAC controllers
Immutable audit trails and forensic exports for compliance and claims
Integration with DCIM, NMS, SOC/SIEM, CMDB and ITSM for unified operational workflows
Book a free consultation with our experts today!
Business benefits
What operators and customers measure
Shieldworkz converts OT security into measurable business outcomes:
Related Use Cases
IIoT Device Security for Smart Data Centers
Data centers are the engines of the modern world, but their reliability no longer rests solely on server uptime and software patches.
Learn more
OT Asset Visibility for Data Center Infrastructure
Modern data centers are the undisputed backbone of global commerce. While enterprises pour immense resources into securing their data and IT networks
Learn more
ICS Network Segmentation for Power Infrastructure
Power infrastructure is the lifeblood of modern industry, serving as the critical foundation for hyper-scale data centers, continuous manufacturing facilities, and smart cities.
Learn more