


Team Shieldworkz
What is a CVE?
Every week, hundreds of new software flaws are discovered across industrial control systems, SCADA platforms, and connected OT devices. Without a common language to name, describe and prioritise those flaws, your security team and the wider industry would be talking past each other, patching different problems, missing critical risks, and wasting time.
Before we commence the deep dive, don’t forget to check out our previous blog post titled What Is a Cyber-Physical System (CPS) here.
That common language is CVE (Common Vulnerabilities and Exposures). Since 1999, CVE has been the universal reference system that lets vendors, governments, researchers and security teams worldwide agree on exactly which vulnerability is being discussed, how severe it is, and how urgently it needs fixing.
In OT and ICS environments where a single unpatched PLC or SCADA server can bring a plant to a standstill or trigger a safety incident, understanding CVE is not optional. It is foundational.
This guide answers every question you have about CVE: what it is, how it works, who runs it, which vulnerabilities qualify, how they are scored, and critically, how Shieldworkz turns CVE intelligence into real-world OT protection.
Why CVE Matters for OT & Industrial Systems
Imagine a critical vulnerability sitting undetected in your plant's SCADA system for six months. Attackers know it exists because it has a CVE identifier and a public entry in the National Vulnerability Database. Your team doesn't, because no one connected the CVE tracking process to your OT environment. That gap is exactly where industrial incidents begin.
Common Vulnerabilities and Exposures (CVE) is the global standard for identifying and naming security vulnerabilities. Since its launch in 1999 by MITRE Corporation, the CVE system has catalogued over 200,000 vulnerabilities and has become the backbone of modern vulnerability management. But in OT, ICS, and CPS environments. Where patching a PLC might mean a 72-hour production shutdown, CVE management is a different challenge entirely.
How Does the CVE System Work?
The CVE lifecycle follows a structured process from discovery to publication. Here is how a vulnerability travels from researcher to remediation:
Stage | Who Acts | What Happens |
1. Discovery | Security researcher / vendor / bug bounty | A new vulnerability is found in software or hardware |
2. Reporting | Researcher contacts CNA or MITRE | Vulnerability details reported via responsible disclosure |
3. Assignment | CNA (CVE Numbering Authority) | A CVE ID is reserved and assigned to the flaw |
4. Analysis | NVD analysts (NIST) | Technical details validated; CVSS score calculated |
5. Publication | NVD / CVE.org | Entry goes public, vendors, tools and teams can act |
6. Remediation | Affected vendors / asset owners | Patches released; organisations apply fixes |
The key players in this process are CVE Numbering Authorities (CNAs). organisations authorised to assign CVE IDs within their scope. Major technology companies like Microsoft, Cisco, Siemens, Rockwell Automation and Schneider Electric are all CNAs, meaning they can issue CVE IDs for vulnerabilities in their own products.
About CVE Identifiers
A CVE identifier follows the format: CVE-[YEAR]-[NUMBER]. For example, CVE-2026-44228 is the infamous Log4Shell vulnerability, a critical flaw in Apache Log4j that affected enterprise and OT systems globally.
Anatomy of a CVE Identifier |
•Format: CVE-YEAR-NUMBER (e.g., CVE-2021-44228) • CVE = Common Vulnerabilities and Exposures programme • 2026 = Year the CVE ID was assigned (not necessarily the year of discovery) • 44228 = Unique sequential number • The ID is permanent, it never changes or gets reused • Referenced consistently across NVD, vendor advisories, SIEM rules, and patch management tools |
Once assigned, a CVE ID becomes the universal reference point across your entire security toolchain, from threat intelligence feeds to firewall rules to vulnerability scanners.
What Qualities Does a Vulnerability Need to Qualify for a CVE?
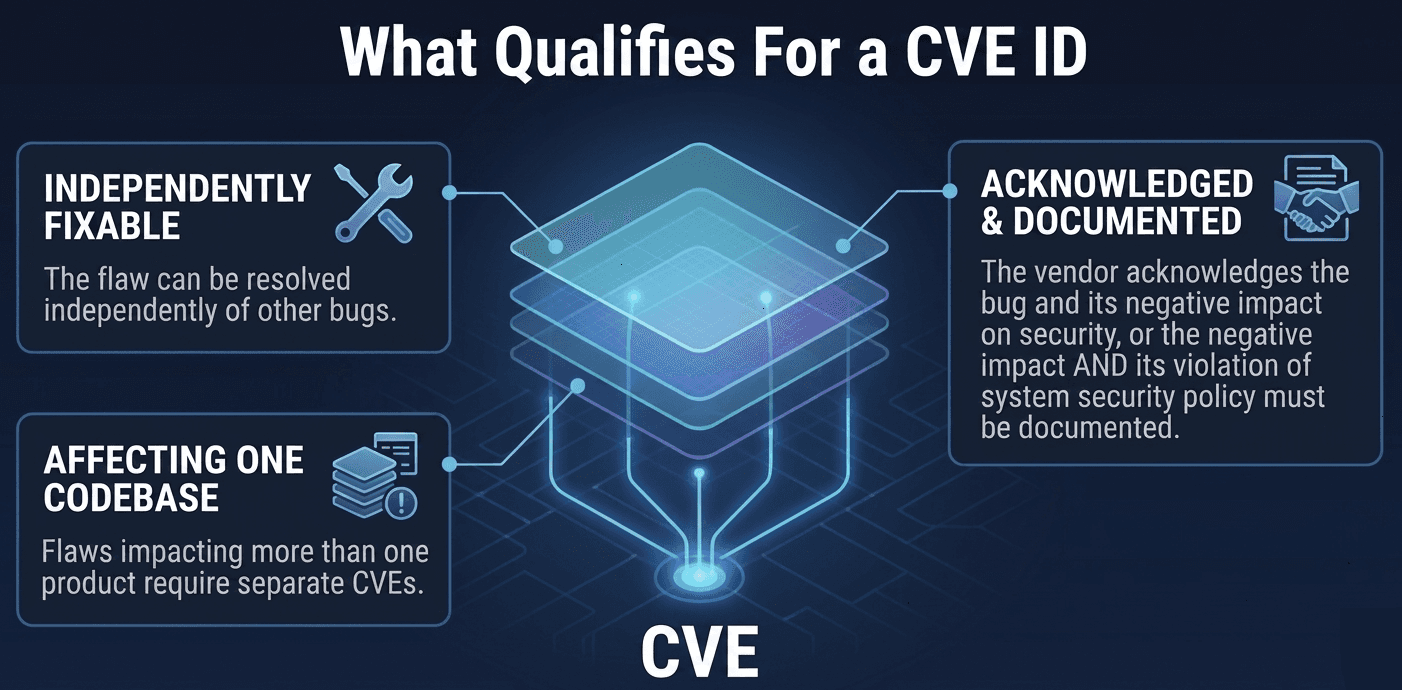
Not every software bug earns a CVE. MITRE applies to three strict criteria. A vulnerability must:
Be independently fixable: The flaw can be patched or mitigated without fixing something else. If two bugs require the same fix, they may share one CVE.
Be acknowledged by the vendor or documented in the public domain: Either the software maker confirms the flaw, or there is credible public evidence (e.g., a working exploit or research paper).
Affect only one codebase: If the same flaw exists in multiple products because of shared source code, each product typically receives its own CVE.
In practice, this means configuration weaknesses, design flaws, and policy issues generally do not receive CVE IDs; those are handled by other frameworks like CWE (Common Weakness Enumeration) or CCE (Common Configuration Enumeration)
What Is the Common Vulnerability Scoring System (CVSS)?
CVSS produces a numerical score from 0.0 to 10.0 mapping to a severity label. The current version is CVSS v3.1, with v4.0 now available. Three metric groups build the score:
Base Score: The intrinsic characteristics of the attack vector, complexity, privileges required, user interaction, and CIA impact.
Temporal Score: Adjusts for exploit maturity (is exploit code publicly available?) and remediation availability.
Environmental Score: Customises the score for your specific environment, critical in OT, where a Medium IT vulnerability may become Critical because it controls a physical process.
A CVE affecting a Windows engineering workstation might score 7.5 (High) in IT. If that workstation runs SCADA software controlling a water treatment plant, the environmental score can push it to 9.8 (Critical). Always contextualise CVSS for your OT environment.
CVSS severity levels and recommended OT response times:
Severity | CVSS Range | OT Action |
Critical | 9.0–10.0 | Patch immediately or halt process |
High | 7.0–8.9 | Patch within 24–72 hours |
Medium | 4.0–6.9 | Patch within 30 days |
Low | 0.1–3.9 | Next maintenance window |
None | 0.0 | No action required |
Who Leads CVE Efforts?
MITRE Corporation: The CVE Programme sponsor and operator, funded by CISA/DHS. Maintains the CVE List and operates the root CNA.
CISA: US federal agency running ICS-CERT, publishing OT/ICS advisories, and maintaining the KEV (Known Exploited Vulnerabilities) catalogue, flagging CVEs actively exploited in the wild.
CVE Numbering Authorities (CNAs): 350+ organisations worldwide authorised to assign CVE IDs, including Microsoft, Cisco, Siemens, Schneider Electric, national CERTs, and bug bounty platforms.
NIST NVD Team: Enriches CVE entries with CVSS scores, CWE classifications, and CPE mappings, transforming raw CVE IDs into actionable intelligence.
Which Vulnerabilities Qualify for a CVE?
Understanding what gets a CVE and what doesn't is critical for OT teams building asset risk registers.
Vulnerabilities That Qualify
Remote code execution (RCE) flaws in firmware or software
Authentication bypass vulnerabilities in ICS protocols (Modbus, DNP3, OPC-UA)
Buffer overflow and memory corruption in embedded systems
SQL injection and XSS in HMI/SCADA web interfaces
Cryptographic weaknesses in industrial device communications
Privilege escalation on engineering workstations
Vulnerabilities That Do NOT Qualify
Insecure default configurations, these are misconfigurations, not vulnerabilities
Denial-of-service caused by normal, expected behaviour
Theoretical or unconfirmed vulnerabilities without a working proof of concept
. Issues in unsupported, EOL OT products that vendors refuse to acknowledge
. Physical security gaps such as unlocked control cabinets
ICS-CERT publishes advisories covering OT vulnerabilities even when no CVE exists, as an important secondary source that Shieldworkz monitors continuously for clients.
Open CVE Databases
These open databases are the starting point for every OT CVE tracking programme:
Key CVE Databases for OT Security Teams |
• NVD (nvd.nist.gov) - Primary US government CVE database with CVSS scores, CPE mappings, and CWE classifications • MITRE CVE List (cve.mitre.org) - The authoritative CVE registry maintained by the CVE Programme • ICS-CERT Advisories (cisa.gov/ics-advisories) - OT/ICS-specific vulnerability advisories from CISA • Vendor Portals - Siemens ProductCERT, Schneider Electric, Rockwell Automation, ABB Cybersecurity • OpenCVE (opencve.io) - Free, open-source CVE monitoring platform with alert subscriptions • Exploit-DB (exploit-db.com) - Open database with public proof-of-concept exploit details |
Map each CVE entry to your OT asset inventory using CPE (Common Platform Enumeration) tags. This turns a generic vulnerability list into a targeted risk register specific to the PLCs, HMIs, and RTUs running in your plant.
Benefits of CVE in OT Cybersecurity
Universal language: CVE IDs allow your CIRT team, OEM vendors, system integrators, and regulators to reference the same vulnerability without ambiguity, eliminating miscommunication during incident response.
Prioritised patching: CVSS scores let OT teams rank vulnerabilities by risk essential when patching live production requires scheduled downtime.
Regulatory compliance: IEC 62443, NERC CIP, and NIS2 all reference CVE-based vulnerability management as a baseline control.
Faster detection: SIEM rules, IDS signatures, and vulnerability scanners are built around CVE IDs, meaning known vulnerabilities trigger alerts automatically.
Supply chain visibility: CVE tracking extends to firmware and third-party components in OT devices, critical for managing supply chain risk.
Audit trail: CVE records create a documented history of known vulnerabilities and remediation actions, essential during post-incident forensics and insurance claims.
Impact of CVE on Vulnerability Management in OT Environments
Effective vulnerability management in OT is not just about knowing what CVEs exist; it is about acting on them without disrupting production. Here is the CVE-powered workflow Shieldworkz recommends:
Step 1- Continuous Asset Inventory
You cannot manage vulnerabilities in assets you do not know exist. Shieldworkz uses passive OT network monitoring to build a live asset register for every PLC, HMI, historian, and engineering workstation, with firmware versions, software versions and network exposure details automatically collected.
Step 2- CVE Correlation
Your asset inventory is continuously correlated against NVD, ICS-CERT advisories, and Shieldworkz's proprietary OT threat intelligence feeds. The moment a new CVE drops for a Siemens S7-1500 PLC and you have that PLC in your environment, you get an alert, automatically, within hours, not weeks.
Step 3- OT-Contextual Risk Scoring
Not every CVE is equal in your environment. Shieldworkz overlays process criticality, network segmentation status, exploitability in the wild, and compensating controls onto the base CVSS score to produce an Operational Risk Score, so your team patches the CVEs that matter most first.
Step 4 - Guided Remediation
For every high-priority CVE, Shieldworkz provides a plain-language remediation guide tailored to OT constraints: patching instructions, compensating controls for systems that cannot be patched (e.g., legacy PLCs on long maintenance cycles), and network segmentation recommendations.
Step 5- Compliance Reporting
Vulnerability management activity is automatically mapped to IEC 62443, NIST CSF 2.0, NERC CIP and NIS2 controls, giving the CISO board-ready evidence of your OT security posture without hours of manual documentation.
The Future of CVEs
CVE 5.0 JSON format: Machine-readable structured format enabling automated ingestion into SIEM, SOAR, and patch management tools.
CVSS v4.0: Adds OT/ICS-specific metrics and improves granularity for cloud-native and embedded system vulnerabilities.
Expanded OT CNA ecosystem: More OT vendors and national CERTs becoming CNAs, reducing time from discovery to CVE publication.
VEX (Vulnerability Exploitability eXchange): New standard allowing vendors to communicate whether a CVE is exploitable in a specific product configuration, critical for OT operators managing thousands of CVEs.
AI-assisted CVE analysis: ML models predicting exploitability, correlating CVEs with threat actor TTPs, and auto-generating detection signatures, accelerating the time from CVE publication to active defence.
Conclusion
CVE is the universal language of vulnerability intelligence, and for OT security teams, fluency in that language is essential. Let us recap the essentials:
CVE (Common Vulnerabilities and Exposures) gives every known software flaw a unique, universally recognised ID, eliminating confusion across teams and vendors.
The CVE lifecycle runs from discovery through CNA assignment, NVD enrichment, publication, and remediation, with 400+ CNAs covering the global software ecosystem.
CVSS scores rate vulnerability severity from 0–10 across Base, Temporal and Environmental metrics, but OT context is essential for accurate prioritisation in industrial environments.
ICS-CERT and Siemens/Schneider CNAs provide dedicated OT CVE coverage. your team should be monitoring these feeds continuously.
Effective CVE-based vulnerability management follows five steps: Inventory → Correlate → Score → Remediate → Report, and Shieldworkz automates all five OT environments.
Emerging trends- CVE 5.0, VEX, SBOM integration and AI-assisted scoring, will make vulnerability intelligence faster, richer and more actionable for OT defenders.
Don't let an unpatched vulnerability halt your production. The gap between CVE discovery and OT remediation is where industrial incidents begin. Stop chasing irrelevant IT alerts and start prioritizing the risks that actually threaten your plant. Book a Demo with Shieldworkz today to see how we turn raw CVE data into automated, OT-safe action plans.
Additional resources
Comprehensive Guide to Network Detection and Response NDR in 2026 here
A downloadable report on the Stryker cyber incident here
Remediation Guides here
OT Security Best Practices and Risk Assessment Guidance here
IEC 62443-based OT/ICS risk assessment checklist for the food and beverage manufacturing sector here
Get Weekly
Resources & News
See How Our Industry-Leading OT Security Solutions Address Critical Security Challenges
You may also like

Top 5 Removable Media Protection Strategies for Critical Infrastructure

Team Shieldworkz

Achieving NIS2 compliance through IEC 62443: A practical guide

Team Shieldworkz

Understanding the Phoenix Contact PLCnext Privilege Escalation Vulnerability

Team Shieldworkz

The Lake Risevatnet Dam Cyberattack: A Stark Reminder That Basic Hygiene Still Defeats Advanced OT Defenses

Team Shieldworkz

10 Peripheral Media Security Controls Every Organization Needs

Team Shieldworkz

USB Malware Protection Strategies for SCADA Systems

Team Shieldworkz










