

Team Shieldworkz
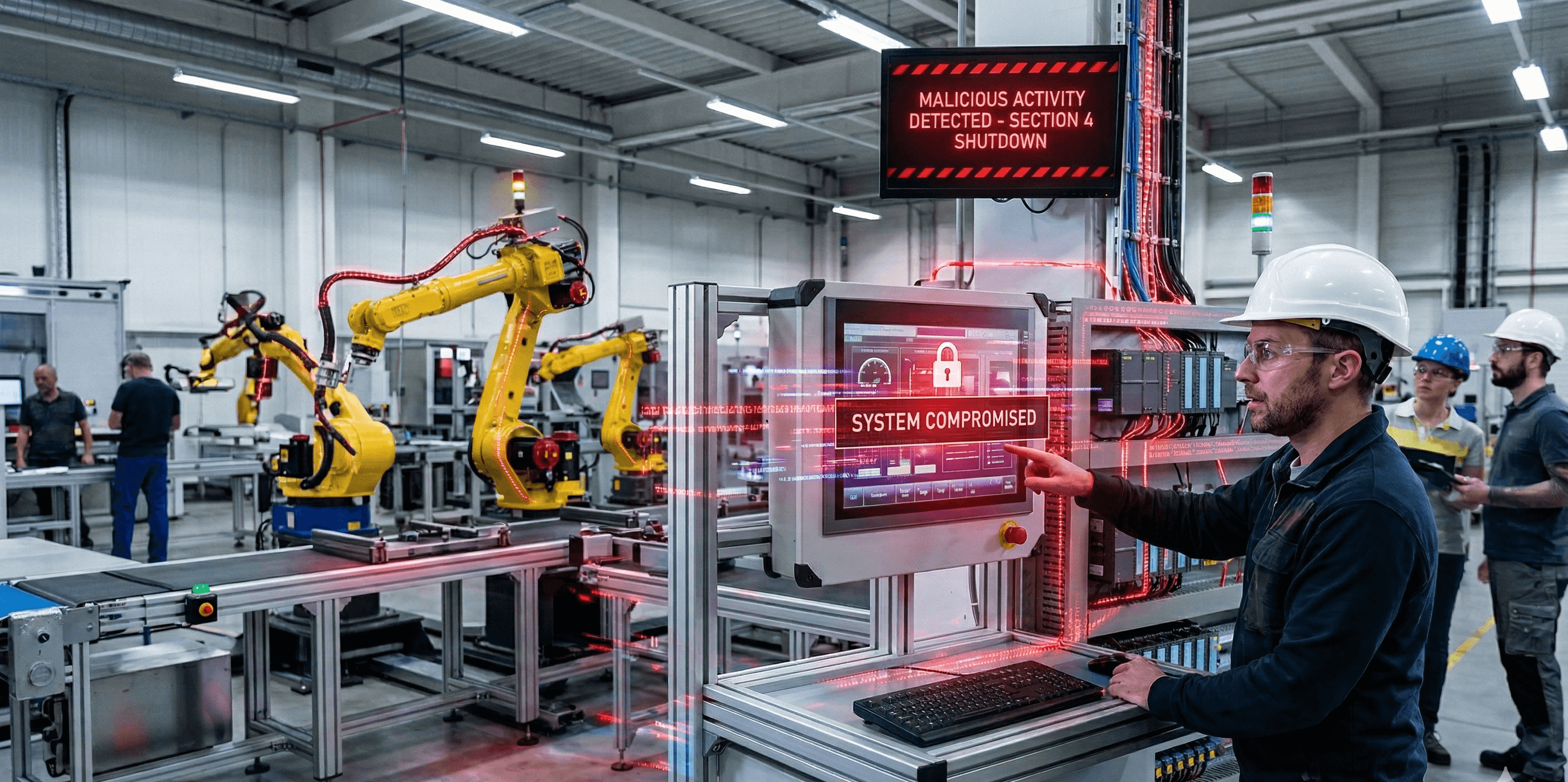
The industrial manufacturing sector is undergoing a massive digital transformation. Connecting the factory floor to the enterprise network unlocks incredible efficiency, predictive maintenance, and real-time analytics. However, this convergence has fundamentally destroyed the traditional air gap that once kept machinery safe from digital harm. Today, the manufacturing floor is a primary target for sophisticated cybercriminals, state-sponsored actors, and insider threats.
OT Security is no longer a niche IT concern; it is a critical pillar of human safety, production uptime, and product quality. A cyberattack on an industrial facility does not just result in a data breach-it halts assembly lines, damages physical equipment, and endangers lives.
To defend your operations, you must understand exactly how adversaries are breaking in. In this comprehensive guide, we break down the top 15 OT Security threats currently targeting the Industrial Manufacturing sector. More importantly, we provide actionable, step-by-step prevention tactics and show you exactly how Shieldworkz can help you secure your industrial ecosystem.
Before we move forward, don’t forget to check out our previous blog post on “Everything you need to know about the Hasbro breach” here
Part 1: The Foundations of Industrial Disruption
The most prevalent OT Security threats rely on exploiting the newly established connections between corporate networks, third-party vendors, and legacy plant machinery.
1. Ransomware and Extortion in OT Operations
Understanding This OT Threat
Ransomware has evolved from a standard IT nuisance into a catastrophic threat to the Industrial Manufacturing sector. These campaigns no longer simply lock computer screens; they actively target industrial control systems, human-machine interfaces, and critical production line infrastructure.
How This Attack Occurs
Cybercriminals infiltrate the industrial environment through phishing campaigns, compromised credentials, or unpatched vulnerabilities. Once inside, they deploy specialized ransomware that disables safety systems or locks programmable logic controllers. Modern attackers utilize double or triple extortion tactics, encrypting operational data while simultaneously stealing sensitive intellectual property. They threaten to release blueprints or launch distributed denial-of-service attacks unless a massive ransom is paid.
Effective Mitigation Strategies
Defending against industrial ransomware requires a defense-in-depth approach. Facilities must establish robust network segmentation to harden the perimeter and prevent lateral movement from IT networks into critical OT environments. Regular, offline backups of programmable logic controller logic, system configurations, and operational data are mandatory to ensure operations can be restored without paying a ransom. Administrators must also implement strict access controls, continuously patch vulnerabilities in internet-facing systems, and conduct routine incident response drills to ensure rapid recovery capabilities.
How Shieldworkz Prevents This
We provide comprehensive protection against ransomware by delivering real-time monitoring and behavioral analytics tailored for industrial environments. The Shieldworkz platform instantly detects anomalous activities, such as unauthorized encryption attempts or irregular lateral movement. By utilizing zero-trust architecture and automated threat isolation protocols, we proactively block malicious actors before they compromise your operational technology, ensuring your manufacturing processes remain resilient and uninterrupted.
2. Supply Chain and Third-Party Vendor Compromises
Understanding This OT Threat
Modern manufacturing relies heavily on external suppliers, maintenance contractors, and vendors. While this ecosystem boosts efficiency, it introduces massive vulnerabilities. Attackers recognize that smaller vendors often possess weaker security postures, making them perfect stepping stones into heavily fortified industrial networks. Because of this, rigorous third-party risk management is now a mandatory security requirement.
How This Attack Occurs
Threat actors bypass your primary perimeter defenses by compromising a trusted vendor. This happens through exploited virtual private networks, shared remote desktop protocols, or stolen credentials used by maintenance personnel. Attackers may also infect legitimate software updates or introduce malware on industrial hardware before it even reaches your facility. Once the compromised vendor connects to your network, attackers silently pivot directly into your OT environment.
Effective Mitigation Strategies
Securing the supply chain demands rigorous industrial vendor security standards for all contractors. Manufacturers must mandate multi-factor authentication for all remote access and enforce the principle of least privilege, ensuring contractors only access the specific machines necessary for their tasks, for a limited time window. Furthermore, organizations must continuously inspect third-party maintenance laptops and USB media for malware before allowing them to connect to internal programmable logic controllers or any critical industrial networks.
How Shieldworkz Prevents This
Shieldworkz eliminates third-party blind spots by strictly enforcing zero-trust network access policies across your industrial ecosystem. Our platform continuously authenticates every remote vendor connection, ensuring complete visibility into third-party activities. By micro-segmenting your network and actively scanning incoming traffic for payloads, we neutralize supply chain threats before they spread.
3. Vulnerabilities in Legacy Systems and Firmware
Understanding This OT Threat
Industrial manufacturing facilities frequently operate on legacy technology designed decades ago. Older programmable logic controllers, human-machine interfaces, and engineering workstations often run on outdated, unsupported operating systems like Windows XP or Windows 7. Because these systems prioritize continuous availability over security, they are rarely patched, leaving massive security gaps.
How This Attack Occurs
Cybercriminals utilize automated scanning tools to identify unpatched vulnerabilities, memory corruption flaws, or default factory credentials within exposed control systems. Because legacy firmware lacks modern security protocols, attackers can easily launch buffer overflow attacks to crash older controllers or deploy zero-day exploits to seize control of the machinery.
Effective Mitigation Strategies
Organizations must meticulously inventory all industrial assets to identify outdated firmware and unpatched software. For instance, legacy Windows HMIs are often susceptible to unpatched operating system exploits, requiring immediate network isolation, internet restriction, and virtual patching. Older controllers frequently suffer from default factory passwords, meaning administrators must enforce credential rotation and disable unused web interfaces. Similarly, unmanaged switches lack traffic filtering capabilities and should be upgraded to managed switches or placed behind an industrial firewall. When physical patching is impossible without halting critical production, manufacturers must employ virtual patching and aggressive network segmentation. Changing all default passwords, restricting physical interface access like USB ports, and disabling unnecessary debug modes are crucial steps to harden these aging environments.
How Shieldworkz Prevents This
Shieldworkz safeguards aging manufacturing infrastructure by deploying advanced virtual patching and deep packet inspection tailored for Industrial Cybersecurity. Our solution creates a protective shield around unpatchable legacy systems, actively blocking exploit attempts without requiring system downtime. We continuously audit device configurations to ensure your vulnerable legacy components remain fully protected.
4. Insecure IT/OT Network Convergence Architectures
Understanding This OT Threat
The push for digital transformation forces the integration of OT with traditional information technology networks. While this convergence enables real-time data analytics, it fundamentally destroys the traditional air-gapped isolation of the factory floor, exposing industrial assets to internet-borne threats.
How This Attack Occurs
Hackers rarely attack OT directly. Instead, they exploit weaker security perimeters on the corporate IT network through phishing or compromised web servers. Because many organizations lack a properly configured demilitarized zone or utilize flat network architectures, attackers face no internal barriers. They easily traverse from the corporate IT environment directly into the industrial control network to alter manufacturing recipes.
Effective Mitigation Strategies
Mitigating convergence risks demands the implementation of the Purdue Model for industrial control system security to structure your networks hierarchically. Manufacturers must build robust demilitarized zones equipped with specialized industrial firewalls to strictly regulate traffic between corporate and factory networks. Enforcing strict network segmentation ensures that a breach in the IT department cannot spread to the production floor. Additionally, administrators should disable direct internet access for all programmable logic controllers and implement continuous monitoring.
How Shieldworkz Prevents This
We secure your convergence strategy by providing dynamic IT/OT network segmentation and intelligent traffic filtering. Our platform seamlessly integrates between your corporate and industrial environments, mapping communication flows to establish an impenetrable boundary. We instantly terminate unauthorized cross-network lateral movement, ensuring enterprise connectivity never compromises operational safety.
5. Insider Threats and Intentional Industrial Sabotage
Understanding This OT Threat
Not all cyber threats originate from external hacking syndicates. Insider threats represent a massive risk because they involve individuals who already possess legitimate access, system knowledge, and physical proximity to critical operations.
How This Attack Occurs
An insider attack bypasses external firewalls completely. A malicious employee might plug a malware-infected USB drive directly into an engineering workstation or intentionally alter safety settings to cause physical damage. A departing engineer might secretly download proprietary blueprints or automated recipes to sell to competitors. Even unintentional threats occur when untrained staff accidentally misconfigure industrial parameters.
Effective Mitigation Strategies
Combating insider threats requires merging robust access management with a strong cybersecurity culture. Organizations must implement strict role-based access controls, ensuring personnel only interact with the systems required for their specific duties. Deploying behavioral analytics tools helps monitor user activity for anomalous actions, such as massive data downloads at unusual hours. Comprehensive, mandatory security awareness training empowers employees to recognize suspicious behavior, while stringent policies restrict unvetted external USB media.
How Shieldworkz Prevents This
Shieldworkz neutralizes insider threats through continuous user behavioral analytics and granular access management engineered for manufacturing environments. Our system establishes baseline behavioral profiles for all operators, immediately flagging and isolating unauthorized actions, such as accessing restricted industrial controllers or attempting unauthorized data exfiltration.
Part 2: The Expanding Attack Surface
As smart sensors and automated protocols flood the factory floor, attackers are finding entirely new ways to manipulate industrial processes.
6. Vulnerabilities in Unsecured IIoT Devices
Understanding This OT Threat
The Industrial Internet of Things provides unprecedented operational visibility. However, smart sensors, wireless actuators, and connected diagnostic tools are often manufactured with minimal security features, lacking basic authentication or data encryption. This expands the industrial attack surface exponentially.
How This Attack Occurs
Cybercriminals actively scan for unsecured IIoT devices exposed to the public internet or utilizing weak wireless protocols like Bluetooth. Because these smart sensors frequently rely on hardcoded passwords or lack firmware update mechanisms, attackers effortlessly compromise them. Once an attacker hijacks a smart sensor, they can manipulate environmental telemetry data, falsely reporting normal temperatures during an actual machine overheating event.
Effective Mitigation Strategies
Securing the IIoT ecosystem requires a zero-trust approach to all connected devices. Manufacturers must meticulously inventory every smart sensor and actuator on the factory floor, promptly changing default credentials upon installation. Facilities should isolate IIoT devices on dedicated network segments, completely separating them from critical industrial control systems and corporate data. Implementing secure, encrypted communication protocols and establishing a routine firmware update schedule are essential practices to ensure these intelligent devices remain secure.
How Shieldworkz Prevents This
Shieldworkz protects your smart manufacturing investments by providing comprehensive device discovery and automated IIoT lifecycle management. We automatically identify every connected sensor, assess its individual vulnerability posture, and continuously monitor its baseline communication patterns. By enforcing strict micro-segmentation and instantly quarantining any device exhibiting irregular behavior, we ensure your operational technology network remains untainted.
7. Man-in-the-Middle Attacks on Industrial Protocols
Understanding This OT Threat
Industrial control networks rely on specialized communication protocols, such as Modbus and Profinet, to transmit commands between human-machine interfaces and programmable logic controllers. Unfortunately, these legacy protocols prioritize speed over security and completely lack inherent encryption or mutual authentication mechanisms.
How This Attack Occurs
In a Man-in-the-Middle attack, a hacker secretly intercepts the network traffic flowing between an engineering workstation and a machine controller. Because the industrial protocol is unencrypted, the attacker easily reads the transmitted data in plain text. More dangerously, the attacker can silently alter the commands. For instance, an operator might send a command to slow down a turbine, but the attacker intercepts and maliciously changes the instruction to accelerate it.
Effective Mitigation Strategies
Defending against industrial protocol exploitation requires implementing modern cryptographic protections where feasible. Manufacturers should transition to secure protocol variants that support encryption and digital signatures whenever upgrading equipment. For existing legacy systems that cannot support encryption, organizations must deploy deep packet inspection firewalls capable of analyzing industrial protocol syntax for anomalies. Hardening network switches to prevent ARP spoofing and restricting physical access to network infrastructure are also absolutely critical defense steps.
How Shieldworkz Prevents This
We eradicate Man-in-the-Middle threats by deploying advanced deep packet inspection customized for native industrial protocols. Our security engine continuously analyzes the granular payload of every Modbus, Profinet, and DNP3 packet, ensuring command integrity and validating source authenticity. If we detect unauthorized command alterations or spoofed network addresses, we immediately sever the compromised connection.
8. Phishing and Targeted Social Engineering
Understanding This OT Threat
While operational technology networks deal with machines, they are ultimately controlled by human operators. Cybercriminals understand that hacking a person is often significantly easier than hacking a firewall. Phishing and targeted social engineering attacks are specifically designed to manipulate human psychology, tricking facility managers and engineers into voluntarily surrendering critical access credentials.
How This Attack Occurs
Attackers conduct extensive reconnaissance on manufacturing employees using social media and corporate websites. They craft highly convincing, AI-driven spear-phishing emails tailored to specific operators. An email might mimic a legitimate urgent alert from an equipment vendor, instructing the engineer to download a critical firmware update. Once the employee clicks the malicious link or opens the infected attachment, credential-harvesting malware is installed on their workstation, granting the attacker legitimate-appearing access.
Effective Mitigation Strategies
Mitigating social engineering threats requires transforming your workforce into a robust human firewall. Organizations must conduct frequent, role-specific cybersecurity awareness training that specifically highlights the dangers of OT-focused phishing attempts. Implementing strict multi-factor authentication across all engineering workstations and remote access portals ensures that stolen passwords alone are useless to attackers. Furthermore, deploying advanced email filtering solutions powered by artificial intelligence can successfully intercept sophisticated phishing campaigns automatically.
How Shieldworkz Prevents This
Shieldworkz combats human-targeted attacks by combining adaptive identity security with continuous endpoint threat detection. Our platform enforces contextual multi-factor authentication, dynamically verifying the identity and device integrity of any operator attempting to access critical industrial controls. Should an employee accidentally execute a malicious phishing payload, our endpoint protection instantly isolates the compromised workstation, preventing lateral movement into the operational network.
9. Data Destruction and Malicious Wiper Malware
Understanding This OT Threat
Unlike traditional ransomware that encrypts files for financial extortion, wiper malware has a singular, devastating objective: total data destruction. In the manufacturing sector, these attacks are often launched by state-sponsored adversaries or hacktivists aiming to cause maximum operational disruption and physical chaos.
How This Attack Occurs
Adversaries deploy wiper malware through compromised third-party supply chains, exploited zero-day vulnerabilities, or highly targeted phishing campaigns. Once inside the operational technology network, the wiper rapidly propagates across connected engineering workstations and human-machine interfaces. It systematically deletes Master Boot Records, erases programmable logic controller configurations, and wipes historical operational databases. Because the primary goal is sabotage rather than financial gain, there is no decryption key offered, leaving facilities completely paralyzed.
Effective Mitigation Strategies
Surviving a wiper malware attack relies entirely on architectural resilience and rigorous data recovery protocols. Manufacturers must maintain isolated, immutable offline backups of all critical machine configurations, recipes, and controller logic. Implementing aggressive network segmentation prevents wiper malware from spreading autonomously across the entire factory floor. Facilities should also develop and frequently test comprehensive disaster recovery plans, ensuring engineering teams can rapidly re-image infected workstations and quickly physically restore operational controllers.
How Shieldworkz Prevents This
We defend against destructive wiper malware through proactive threat hunting and immutable system safeguards. Our platform continuously monitors the industrial network for the specific behavioral signatures associated with mass file deletion and unauthorized boot record modifications. By deploying automated containment protocols, Shieldworkz instantly isolates infected segments at the first sign of destructive activity.
10. DDoS Attacks on Legacy ICS Infrastructure
Understanding This OT Threat
Distributed Denial of Service attacks are designed to overwhelm a system with a massive flood of artificial network traffic. While modern enterprise IT servers can often absorb these traffic spikes, legacy industrial control systems are incredibly fragile. Older programmable logic controllers and industrial network switches were built for low-bandwidth, highly predictable traffic, making them exceptionally vulnerable to even minor network floods.
How This Attack Occurs
Cybercriminals command massive botnets-often composed of compromised IIoT devices-to blast a targeted manufacturing facility's external IP addresses or internal industrial network with overwhelming data requests. Because legacy industrial controllers possess very limited processing power and small memory buffers, the flood of traffic causes them to instantly crash or drop critical command packets. This results in the complete loss of visibility for human operators, halting automated assembly lines and critical monitoring.
Effective Mitigation Strategies
Defending industrial environments against DDoS attacks requires robust network traffic management and a rapid incident response plan. When an attack occurs, security teams must quickly identify the source to determine if the malicious traffic is external or originating from compromised internal IIoT devices. Administrators should instantly activate rate limiting by engaging network perimeter DDoS mitigation hardware and segment the affected production zone to protect the wider plant floor. Additionally, industrial firewalls must be configured to automatically drop malformed packets or anomalous broadcast storms. Crucially, manufacturers should ensure that critical industrial control systems are never directly exposed to the public internet to limit external attack surfaces.
How Shieldworkz Prevents This
Shieldworkz neutralizes DDoS threats by delivering intelligent traffic shaping and continuous availability monitoring for your critical operational technology. Our platform dynamically analyzes incoming network loads, automatically filtering out malicious traffic floods while ensuring legitimate industrial command packets are prioritized and delivered without latency. By continuously auditing the processing health of your legacy controllers, we guarantee that your delicate industrial infrastructure remains online and responsive.
Part 3: Advanced Cyber-Physical Sabotage
The cutting edge of industrial cybercrime goes beyond shutting down networks. Attackers are now attempting to alter the physical reality of the products being manufactured.
11. Product-Oriented Geometric Sabotage (Cyber-to-Physical Attacks)
Understanding This OT Threat
As manufacturing becomes fully digitized, attackers are shifting focus from simply stopping production to actively altering the products themselves. Cyber-to-Physical attacks target the geometric and material integrity of manufactured parts. By making nearly invisible changes to a product’s design, attackers can compromise its structural strength, leading to catastrophic physical failures when the part is later used in the field.
How This Attack Occurs
Adversaries infiltrate the engineering network and quietly tamper with digital files, such as computer-aided design models or G-code tool paths. Instead of crashing the machine, they alter critical process parameters-like the movement of a CNC nozzle or the extrusion rate in 3D printing. They might insert microscopic voids into high-stress areas of a component. Because these alterations do not drastically change overall machining time or power consumption, they frequently evade standard process monitoring tools.
Effective Mitigation Strategies
Manufacturers must implement strict file integrity monitoring and digital watermarking to ensure design files remain untouched. Deploying localized, in-situ process monitoring techniques that specifically look for granular, localized changes in machine behavior is critical for detecting these subtle geometric alterations before faulty parts are finalized.
How Shieldworkz Prevents This
Shieldworkz utilizes advanced file integrity analytics and behavioral baselining tailored for the engineering floor. By continuously authenticating digital design files and monitoring the exact execution parameters of your PLCs, our platform instantly flags any unauthorized deviations in G-code or CAD execution, ensuring that your final products perfectly match their intended specifications.
12. Quality Control (QC) System Subversion
Understanding This OT Threat
Traditionally, cybersecurity focuses on protecting the production line itself. However, adversaries are increasingly targeting the Quality Control and inspection systems that serve as the final safety net for manufactured goods. If the inspection system is compromised, attackers can force the facility to discard perfectly good products or, far worse, ship dangerously defective components to clients.
How This Attack Occurs
Instead of attacking the product design or the physical production machinery, cybercriminals exploit vulnerabilities directly within the automated QC software. They can maliciously alter the Geometric Dimensioning and Tolerancing information or change the acceptable thresholds for part quality definitions. By manipulating these digital thresholds, the compromised QC system will falsely designate maliciously altered or structurally faulty parts as accepted and conforming to standards.
Effective Mitigation Strategies
Organizations must expand their attack surface modeling to explicitly include all quality inspection tools. QC networks should be heavily segmented from both corporate IT and general production OT networks. Implementing strict, dual-authorization requirements for any changes to inspection parameters and routinely auditing QC software against offline metrology standards are essential steps to maintain integrity.
How Shieldworkz Prevents This
Shieldworkz extends its zero-trust architecture directly into your metrology and quality assurance labs. We monitor the data pipelines feeding your automated inspection systems to prevent unauthorized tampering with tolerance limits. By isolating QC tools and validating the integrity of inspection reporting, we ensure that your quality control safety net remains completely untampered and trustworthy.
13. Side-Channel Espionage and Reverse Engineering
Understanding This OT Threat
Not all attacks rely on injecting malicious code; some merely listen. Side-channel analysis is a highly sophisticated form of industrial espionage where attackers steal valuable intellectual property by monitoring the physical emanations of your manufacturing equipment. This threat requires no direct network breach of your core industrial control systems.
How This Attack Occurs
Every physical manufacturing process-especially high-end Additive Manufacturing or precision CNC machining-emits distinct physical fingerprints, such as specific acoustic signatures, vibrations, and thermal outputs. Attackers place covert listening devices, or compromise unsecured IIoT microphones nearby, to capture these process dynamics variables. They then use advanced algorithms to reverse-engineer these signals, completely reconstructing your proprietary 3D object models and trade secrets.
Effective Mitigation Strategies
Combating side-channel espionage requires bridging physical and cybersecurity. Facilities manufacturing highly classified or proprietary components should invest in acoustic dampening and strict physical access controls. From a technical standpoint, deliberately injecting acoustic or vibration noise during production can effectively obfuscate the true signals, preventing adversaries from successfully retrieving accurate side-channel information.
How Shieldworkz Prevents This
While side-channel attacks exploit physical emissions, Shieldworkz helps by securing the surrounding digital environment. Our platform continuously scans your network for unauthorized rogue IIoT sensors or compromised devices attempting to exfiltrate massive, continuous streams of audio or vibration data. We block the digital pathways adversaries use to send stolen physical intelligence out of your facility.
14. False Data Injection Attacks (FDIA) on Telemetry
Understanding This OT Threat
Industrial operators rely entirely on the telemetry data displayed on their human-machine interfaces to safely manage complex processes. False Data Injection Attacks aim to blind or deceive these operators by maliciously altering the data traveling between the physical sensors and the central control systems.
How This Attack Occurs
Once inside the OT network, attackers intercept the communication lines from sensors measuring critical metrics like temperature, pressure, or rotation speed. They actively inject falsified data into this stream. For example, if adversaries are physically tampering with a production process or causing a machine to dangerously overheat, they will simultaneously inject normal sensor readings into the network. The human operators looking at the HMI will see perfectly nominal operations, completely unaware that a physical disaster is unfolding on the factory floor.
Effective Mitigation Strategies
Relying on unencrypted legacy sensor data is highly dangerous. Facilities must deploy secure, authenticated communication protocols for all critical telemetry. Furthermore, implementing unique physical device fingerprinting techniques can help control systems verify that incoming data is actually originating from the legitimate sensor, rather than a spoofed endpoint injected by an attacker.
How Shieldworkz Prevents This
Shieldworkz actively defeats FDIA through rigorous deep packet inspection and cross-sensor behavioral correlation. Our analytics engine constantly cross-references data points across your industrial environment. If a temperature sensor reports normal heat levels while the corresponding power consumption spikes, Shieldworkz instantly detects the logical discrepancy, flags the injected data, and alerts operators to the hidden anomaly before physical damage occurs.
15. Physical-to-Cyber (P2C) Sensor De-calibration
Understanding This OT Threat
Cybersecurity often focuses strictly on digital perimeters, but the convergence of IT and OT means that physical hardware is now an attack vector for the digital network. Physical-to-Cyber attacks occur when an adversary manipulates the physical components of the manufacturing system to intentionally trigger malicious software responses or disrupt automated digital logic.
How This Attack Occurs
This attack often requires an insider or physical proximity to the machines. An attacker physically tampers with the manufacturing equipment-for instance, manually de-calibrating a critical sensor so it modifies its input signal. Because modern smart manufacturing systems rely on real-time, data-driven adaptive control, this intentionally skewed physical data feeds directly into the programmable logic controllers. The automation software, reacting to the bad physical input, makes catastrophic adjustments, halting production or damaging tools.
Effective Mitigation Strategies
Mitigating P2C threats requires a convergence of physical security and OT resilience. Hardware should feature tamper-evident seals, and physical access to sensitive calibration nodes must be strictly limited and logged. Additionally, engineering teams must design automation logic with robust fault-tolerance, ensuring that a sudden, extreme shift from a single sensor triggers a safe-mode pause rather than a destructive automated compensation.
How Shieldworkz Prevents This
Shieldworkz bridges the gap between digital and physical threats by establishing strict baseline behaviors for all industrial inputs. If a sensor suddenly begins transmitting radically altered data outside of historical physical norms-indicative of manual de-calibration or tampering-our platform immediately alerts security teams. We ensure that anomalous physical inputs are quarantined before they can corrupt your broader automated decision-making processes.
Conclusion
The threats facing the Industrial Manufacturing sector have moved far beyond standard IT malware. From ransomware locking critical programmable logic controllers and vendor supply chain compromises, to highly sophisticated cyber-physical attacks designed to alter product geometry and falsify quality control data, the stakes have never been higher.
Protecting your facility requires shifting your mindset. You can no longer rely on outdated air gaps or basic IT firewalls. You must build a resilient, defense-in-depth architecture that provides total visibility, continuous behavioral monitoring, and automated threat isolation across both legacy systems and modern IIoT networks.
When you implement rigorous network segmentation, control third-party access, and utilize advanced deep packet inspection tailored for industrial protocols, security transforms from a compliance headache into a true driver of operational resilience.
Additional resources
A downloadable report on the Stryker cyber incident here
Remediation Guides here
OT Security Best Practices and Risk Assessment Guidance here
IEC 62443-based OT/ICS risk assessment checklist for the food and beverage manufacturing sector here
Get Weekly
Resources & News
See How Our Industry-Leading OT Security Solutions Address Critical Security Challenges
You may also like

OT Asset Visibility and IEC 62443: Building a Compliant ICS Security Posture This Year
Team Shieldworkz

Best Operational Resilience Platforms Categories for Critical Infrastructure in 2026

Team Shieldworkz
New NIST SP 1800-41 draft: Reinforcing cyber resilience in manufacturing OT environments
Team Shieldworkz

Third-Party Cyber Risks in OT Environments: Why Industrial Network Monitoring Must Go Beyond the Perimeter in 2026

Team Shieldworkz

Top 7 Critical Infrastructure Cybersecurity Challenges and Solutions

Team Shieldworkz

How Zero Trust Network Access Secures OT Environments

Team Shieldworkz









