


Team Shieldworkz
We are dealing with a threat environment that is constantly in a flux. On the one hand, we have threat actors and hacktivists openly naming companies they are targeting, while on the other hand, security teams in enterprises are dealing with distractions within and without. Further, Ransomware-as-a-Service (RaaS) now targets proprietary industrial protocols, and geopolitical tensions have turned power grids and water treatment plants into primary theatres of operation.
To defend critical infrastructure, we cannot rely on IT-centric "patch-and-pray" methods. We must lean into the IEC 62443 standard to derive the right controls and framework-based interventions to ensure the infrastructure is always protected.
Defining the perimeter: The zone and conduit model (IEC 62443-3-2)
The most common failure in modern OT environments is a fully "flat" network. If an attacker gains access to a guest Wi-Fi in the corporate office and can move laterally to a Programmable Logic Controller (PLC) on the factory floor, the architecture has failed. Further, if the security teams are unable to spot this movement or isolate an infected device or zone, the security posture has failed.
Zones: Group assets based on their criticality, security and/or functional requirements and assign a zone security owner. To give you an idea of how to identify zones, a safety-instrumented system (SIS) should never reside in the same zone as a basic process control station.
Conduits: These are the communication paths between zones. By strictly controlling conduits with deep-packet inspection (DPI) and stateful firewalls, you can prevent lateral movement.
Actionable step: Conduct a high-level risk assessment to define your Security Levels (SL-Target) for each zone. For critical infrastructure, aim for SL-3 or SL-4, which assumes an adversary with high motivation and IACS-specific skills.
Defensive controls: Moving beyond the perimeter (IEC 62443-3-3)
Once your zones are defined, you must apply system-level requirements. In the current threat climate, "Assumed Breach" is the only logical mindset.
Foundation Requirement 1: Identification and Authentication Control (IAC). Implement multi-factor authentication (MFA) for all remote access. Password-sharing for HMI accounts is an open door for modern malware.
Foundation Requirement 2: Use Control (UC). Enforce the Principle of Least Privilege. Users and processes should only have the permissions necessary to perform their specific tasks.
Foundation Requirement 5: Restricted Data Flow. This is where Network Detection and Response (NDR) becomes critical. You must have visibility into East-West traffic within the OT environment to spot anomalies that signal a reconnaissance phase.
Managing the residual risk: The hard truth
Even with the most rigorous application of IEC 62443 controls, residual risk—the risk that remains after all security measures are implemented—will exist. In OT, this is often driven by:
Legacy Assets: Devices that cannot support encryption or modern authentication.
Supply Chain: Vulnerabilities embedded in third-party firmware (the "SolarWinds" of the OT world).
Human Error: Phishing remains the primary vector for initial access.
The strategy: Compensating controls are your best friend. If an aging PLC cannot be patched, isolate it behind a dedicated industrial security appliance or use unidirectional gateways (data diodes) to ensure data only flows out for monitoring, never in.
Implementation checklist for security leaders
Inventory everything: You cannot even think of protecting what you cannot see. Use passive discovery tools to build an automated Asset Inventory.
Patching vs. Protection: Acknowledge that 100% patching is impossible in OT. Focus on "Virtual Patching" via IPS/IDS for vulnerabilities that cannot be addressed during production cycles.
Incident Response (IR): Develop OT-specific playbooks. An IT playbook that says "wipe and restore" can lead to catastrophic physical outcomes in a chemical plant.
The IEC 62443 KPI Tracker
To manage what you measure, use this tracker to communicate progress to the board and technical teams.
KPI Category | Metric | Frequency | Goal |
Visibility | % of OT assets identified and categorized in the Asset Inventory. | Monthly | 100% |
Segmentation | Number of cross-zone conduits without firewall/DPI enforcement. | Quarterly | 0 |
Vulnerability | Mean Time to Mitigate (MTTM) critical vulnerabilities in OT zones. | Monthly | < 30 Days (via patch or virtual patch) |
Access Control | % of remote access sessions utilizing MFA and Jump Hosts. | Monthly | 100% |
Resilience | Time to recover a "Golden Image" for a critical HMI/Workstation. | Bi-Annually | < 4 Hours |
Risk | Percentage of legacy assets covered by "Compensating Controls." | Annually | 100% |
To sum it up,
The deterioration of the threat environment is a call to action, not a cause for despair. By adopting the lifecycle approach of IEC 62443—from design to operation—we can build infrastructure that is not just secure, but resilient enough to withstand the "black swan" events of tomorrow.
Stay vigilant, stay segmented.
Schedule an IEC 62443-based automated assessment
Additional IEC 62443 resources from Shieldworkz for OT security teams
Access Shieldworkz IEC 62443 Remediation Guides
IEC 62443-Based OT/ICS Risk Assessment Checklist for Renewable Energy Operators
IEC 62443-Based Risk Assessment Checklist for Airport Operations and Critical Infrastructure
IEC 62443 Compliance Performance Scorecard and OT Cybersecurity KPI Calculator
IEC 62443-Based Zoning Implementation and Validation Checklist
Strategic Implementation of ISA/IEC 62443-3-2
IEC 62443 and NIS2 Compliance Checklist
Get Weekly
Resources & News
See How Our Industry-Leading OT Security Solutions Address Critical Security Challenges
You may also like
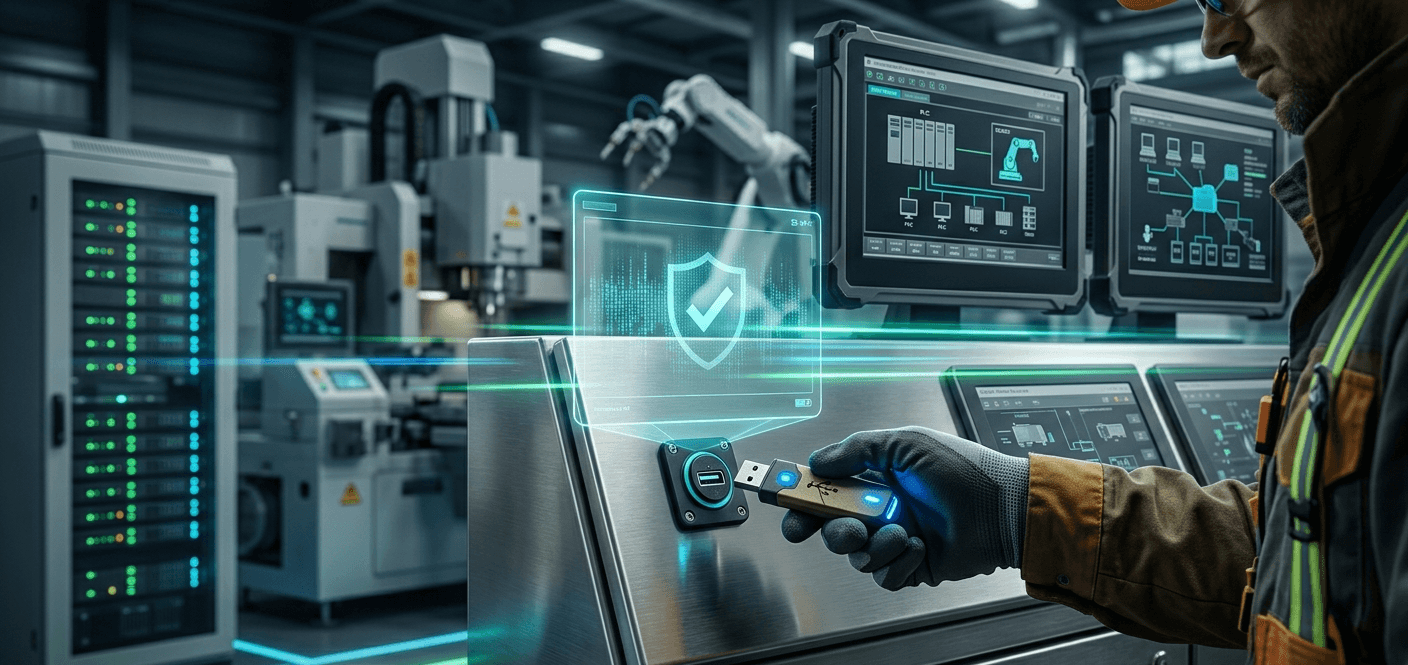
Best USB Device Control Software for OT Networks

Team Shieldworkz

The USB drive that could shut down a refinery

Team Shieldworkz

The Ultimate Guide to Zero Trust Security for Industrial Control Systems

Team Shieldworkz

SCADA Security: Why Removable Media Is One of the Biggest Attack Vectors in OT Environments

Team Shieldworkz

Navigating Removable Media Compliance: NERC CIP & IEC 62443 for OT/ICS Environments

Team Shieldworkz
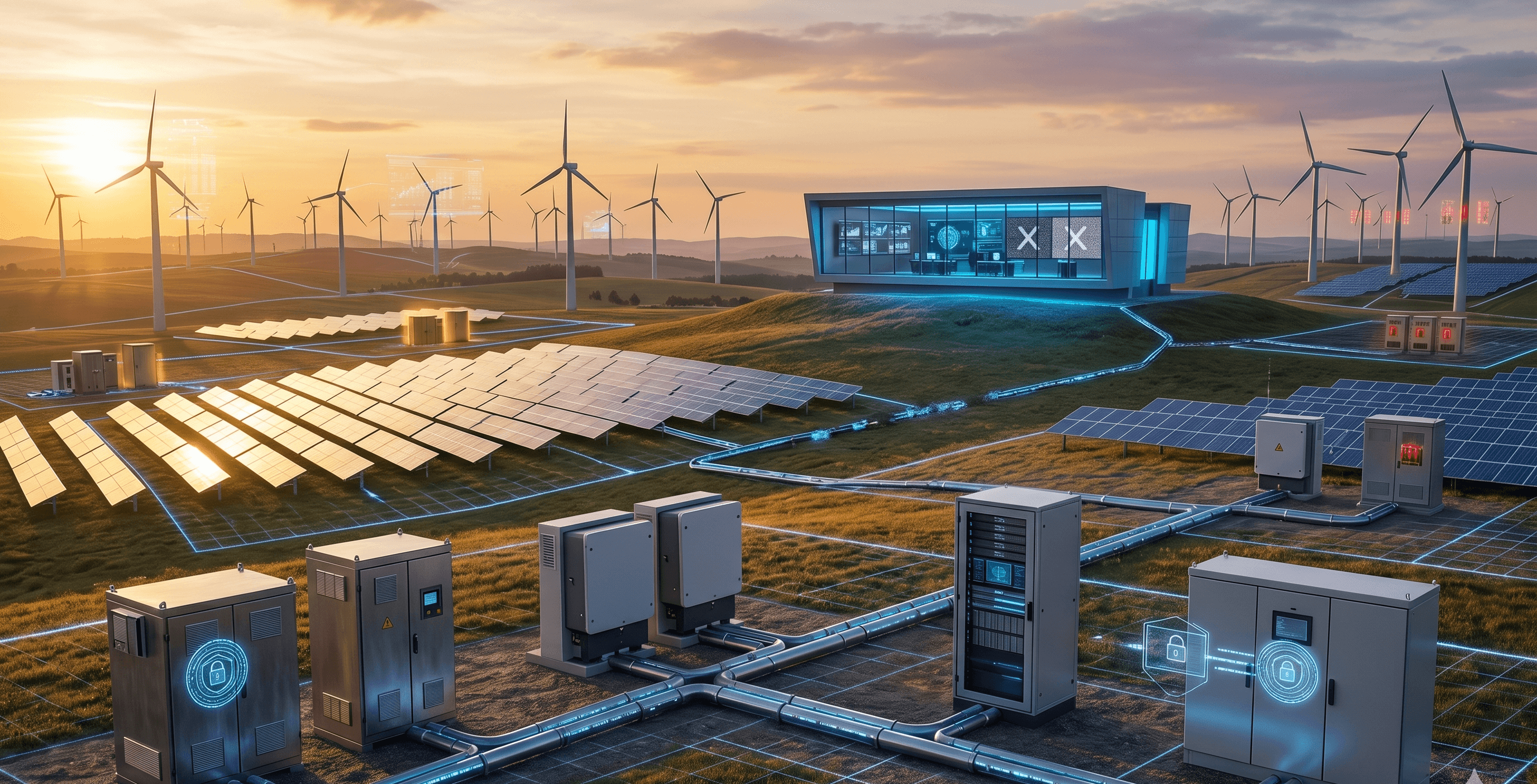
Securing the Distributed Grid: Lessons from the First Coordinated Cyberattack on Wind and Solar Infrastructure

Team Shieldworkz








